WebRTC Leak Tool
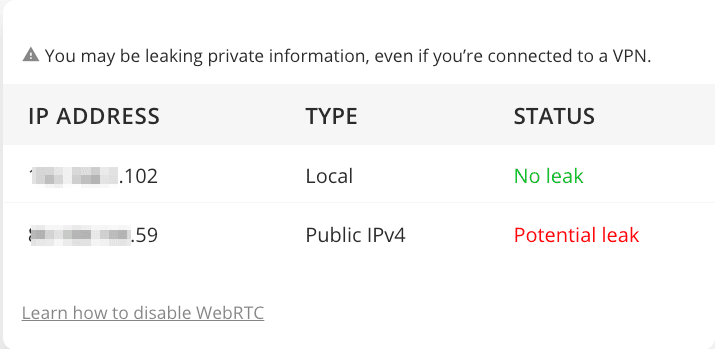
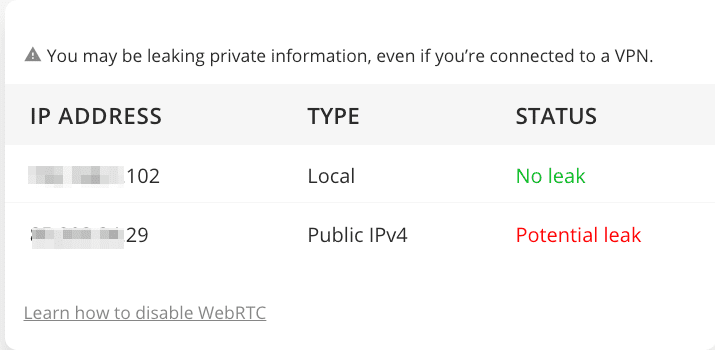
Your browser is exposing these IPs to websites you visit:
Nowadays, internet users have been learning several ways to ensure their online privacy. But what if there’s something that can compromise that without you even knowing? What if it’s embedded way deep in your browser – leaking your public IP address while you’re in the dark? It is possible if your browser has WebRTC. Read on to find out all about WebRTC, its data leaking, and how to fix it below.
What’s WebRTC
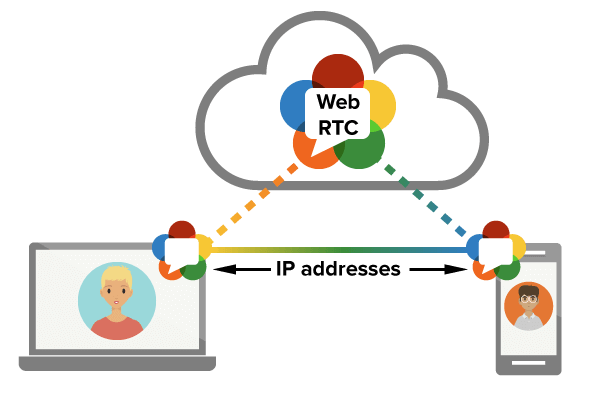
Short for Web Real-Time Communication, WebRTC is an open-source tool (HTML5) that you can use to add real-time peer-to-peer, media communications directly between browsers.
WebRTC saw the light in 2011 and has grown in popularity throughout the years. In 2016, WebRTC had quite a year reaching two billion Chrome browsers and one billion WebRTC audio/video minutes per week on them. The open-source project is entirely free. But if you use it, you should always keep an eye on it since it’s constantly evolving and improving.
Although I mentioned what it does, WebRTC is still capable of so much more. WebRTC helped create a variety of open-source projects and frameworks. There are about 1200 WebRTC-based companies and projects around the world. If you don’t know yet, the open-source is available on Mozilla, Chrome, Opera, and Safari.
Remember back in the day when someone wanted to create anything that allowed voice or video-calling? Yeah, they most probably used C/C++ in the process. It was a popular, yet expensive option at the time. However, WebRTC changes all that as it takes the need for C/C++ and replaces it with a Javascript API.
Seems Great – Not Quite
As grand as it is, you should know by now that nothing on the internet can come without drawbacks. Since you’re sharing your IP addresses directly with another browser, it could allow third-party websites to detect your IP address. They can use that to identify you and pinpoint your actual location. That’s exactly what we call a WebRTC Leak.
Your location isn’t the only thing jeopardized with an IP leak. No, all of your browsing activities can be monitored as well. That’s how your ISP keeps tags on what you do online, by the way. If your IP is out in the open, your identity also is. That way, any hacker can tap into your private information including bank accounts, emails, passwords, and of course, exact location.
How to Block WebRTC Leaks
There are two ways to block WebRTC leaks from occurring. The first method is to use a Virtual Private Network. This will hide your real IP address and replace it with a different one as long as a VPN connection is present. As a result, if you’re public IP is leaked, you’ll be safe all the time as it’s not your actual one, to begin with.
On the other hand, WebRTC can be deactivated manually. It’s a bit of a daunting task, but it’s still doable. Let me show you how you can do so using both methods.
VPN Method
This one is pretty easy to go through. All you need is a VPN connection, and you’re good to go. Here’s how it all goes down:
1. First, when you use the WebRTC leak tool above without a VPN, you’ll notice that there might be a possible leak.
3. Download and install their VPN application on the device you’re using. Clients are available on Android, PC, Mac, and iOS. You’ll also find extensions for Chrome and Firefox.
4. After that, sign in with your account and connect to a VPN server.
5. If you want to make sure that your VPN connection has established, check this IP Verifier.
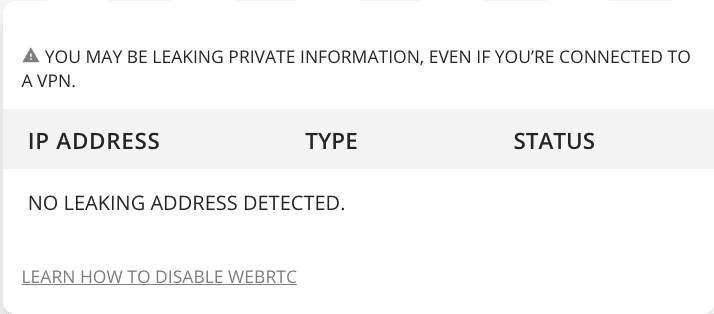
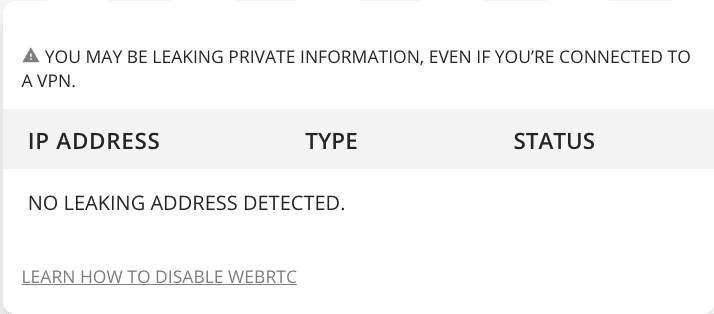
6. Now, use the WebRTC leak tool above once more. You’ll get this.
Browser Method
If you’re a Firefox, Chrome, and Opera user, you’re most vulnerable to WebRTC leaks. That’s because these browsers have the open-source enabled on them by default. If you want to disable it manually, you should know that it will terminate WebRTC’s functionality completely. Let’s begin:
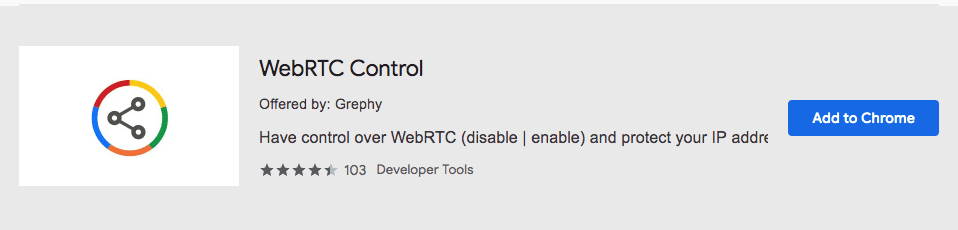
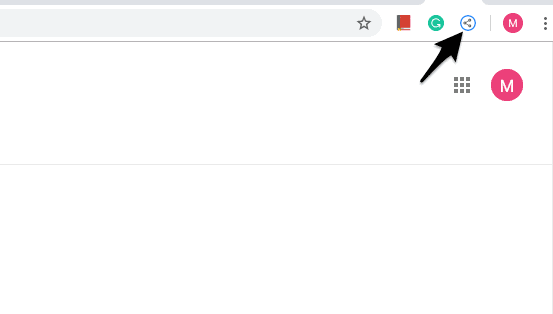
Chrome Browser
Here’s what you need to do when you’re using Google Chrome:
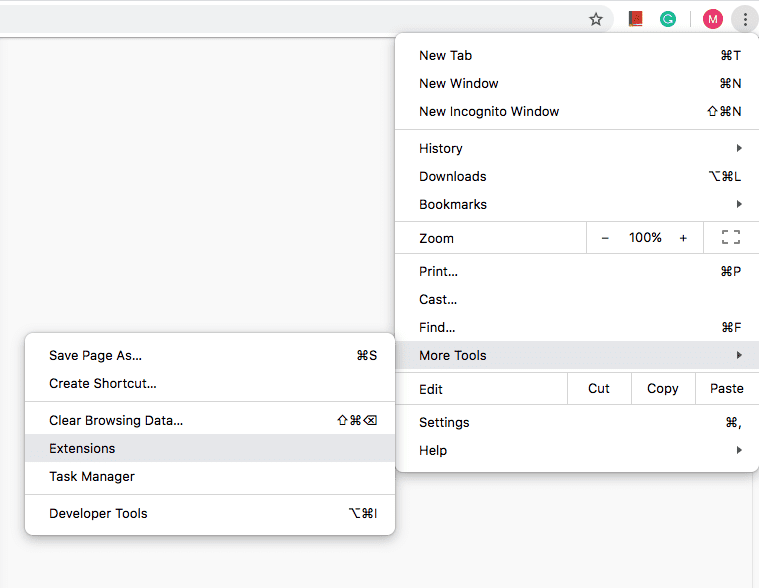
1. To start the process, click on the three dots on the top right of your browser.
2. Next, go to More Tools -> Extensions.
4. Download the extension to your browser.
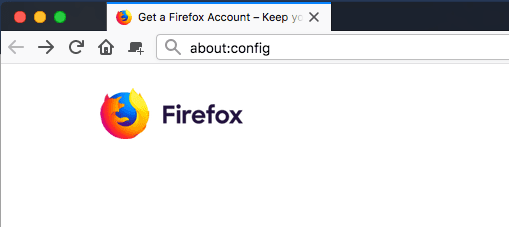
Mozilla Firefox Browser
As for Firefox users, you can deactivate WebRTC by following these steps:
1. Open your Firefox and type “about:config” without the quotations.
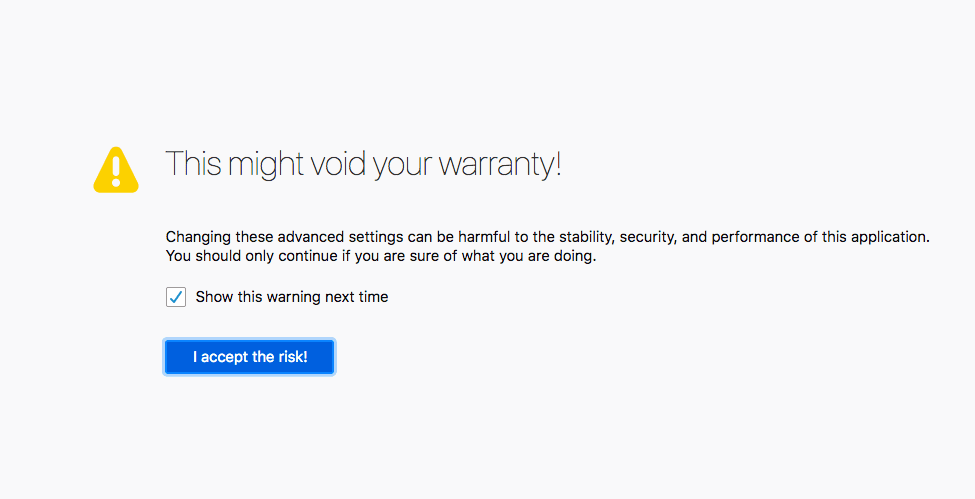
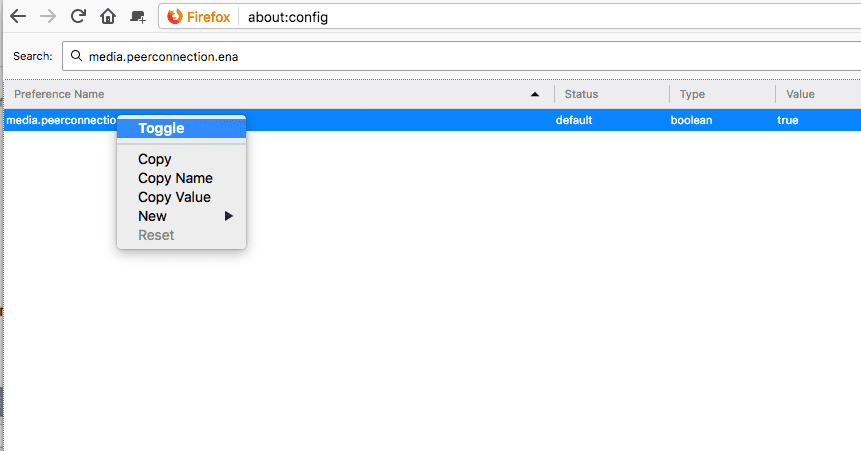
3. On the next page, you’ll find names that might be hard to comprehend. Just type “media.peerconnection.enabled” in the search bar.
4. Once you get it, right-click on the title and hit Toggle.
6. Finally, check the WebRTC leak tool on Firefox. You’ll notice that no data is being leaked.
Is Blocking WebRTC Enough Though?
No, it’s not. It might be a good way to start securing your online activities, but still, you need more. If you use a VPN’s application or web extension, you won’t have to worry about any WebRTC leak at all. You’ll be using a different IP address in the process, which makes it next to impossible for your real identity to be revealed. Don’t risk it, follow the steps provided in the guide above and you’ll be just fine.




