S1deload and SYS01 Stealers: A Well-Executed Malverposting Campaign
The year 2023 has had its fair share of cyberattacks all over the world. Threat actors are not sitting around waiting for the right moment to strike. No! They’re elevating their techniques to increase their success rates. We’ve all heard of malvertising tactics – they’re pretty common. Well, now, users are facing another threat in the form of Malverposting.

The use of malverposting isn’t new, but it’s not that common as well. Apparently, Vietnamese threat actor is popularizing this technique once more by infiltrating over 500,000 devices worldwide over the past three months.
The threat is serious, considering the fact that this particular campaign is spread through Facebook. And we all know how global the platform is. How is the threat actor implementing this campaign? What can the stealers do? Here’s what we know.
Malverposting – Pay a Little, Gain a lot
As we mentioned, cybercriminals have been coming up with new ways and methods to infiltrate their victims’ devices.
Malvertising is a very good tactic as not everyone can suspect and detect that what they’re clicking on is fake and malicious.
In fact, this technique saw a spike in activity about a week ago. Threat actors made use of Google Ads to spread LOBSHOT malware across devices. This particular campaign roamed Google using fake ads impersonating the likes of AnyDesk.
Now, instead of using Google, the malicious actors are taking advantage of how impactful social media has become, spreading their practices on the likes of Facebook and Twitter.
Before we dive into details, here’s how the entire campaign takes place in a nutshell:
“Malverposting, the use of promoted social media posts and tweets to propagate malicious software and other security threats — is on the rise.
One of those campaigns, linked to a Vietnamese threat actor, has been ongoing for months now gaining more traction lately using resilient deployment techniques and is estimated to surpass 500k infections worldwide so far.
Yet, the initial enabler for those numbers is the abuse of Facebook’s Ads service as the first stage delivery mechanism responsible for this mass propagation.“
Source: Guardio Labs
Posting on Facebook can get threat actors a lot of attention and clicks. The term Malverposting is quite clear – utilize social posts for malicious practices such as propagating malware and other threats.
To reach a broader audience, the threat actors have to pay to “amplify” their posts. And in this campaign, that’s exactly what they did.
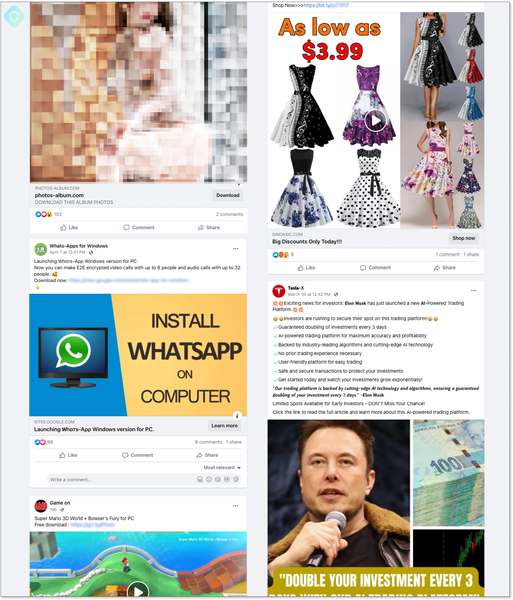
These posts contain some sort of zip files to download. Well, at least some of them give the impression of having something to offer via “Download.”
Once the victim executes the zip files, the infection chain commences, and the stealer malware takes root, siphoning session cookies, account data, and other information in the process.
S1deload and SYS01 stealers are dangerous, and each one has its own capabilities. Sideload can hijack users’ social media accounts and mine cryptocurrency.
SYS01, on the other hand, is somehow similar, as it has the ability to harvest Facebook cookies from Chromium-based web browsers, exfiltrate Facebook data to a remote server, and download/run arbitrary files.
A New Campaign with Risky Capabilities
The stealers can easily hijack Facebook accounts, which makes pushing more sponsored posts quite easy – no need to boost anything anymore. This will definitely scale the scheme further.
So far, the study shows that this campaign’s majority of victims reside in Australia, Canada, India, the U.K., and the U.S.
However, with such capabilities, things can get worse very quickly. The stealers are evolving to incorporate more detection evasion features – be careful what you click on from now on.





