RATDispenser Malware – A Stealthy Trojan Targetting Windows PC
With cybercrime on the rise, attackers are finding new ways to track specific victims and infect their devices with all sorts of malware. The most common way would be phishing emails, which TikTok profiles suffered from a while back.
Using remote access trojans (RATs) in phishing attacks has become a very common practice lately among cybercriminals. And now, a new stealthy JavaScript loader named RATDispenser has surfaced, targeting none other than Windows PCs.
Attackers have one thing in mind behind such an attack and it is to steal information and give them control over the target devices. So, who discovered the campaign, and how does it operate? Find out in this comprehensive news article.
RATDispenser – Email, Infect, Control
Cybercriminals have always developed enhanced stealthy ways to take over their victims’ devices. The HP Threat Research team found the malware and according to their report, it has an 11% detection rate.
It can easily evade security controls and deliver malware without the need to communicate with an actor-controlled server (it’s used as a first-stage malware dropper).
To make things worse, the JavaScript loader established distribution partnerships with at least eight malware families.
Just like any other JavaScript malware attack, RATDispenser doesn’t directly take control over the compromised device. Instead, the attackers use it to gain an initial foothold on the system first, then it launches a secondary malware to complete the task.
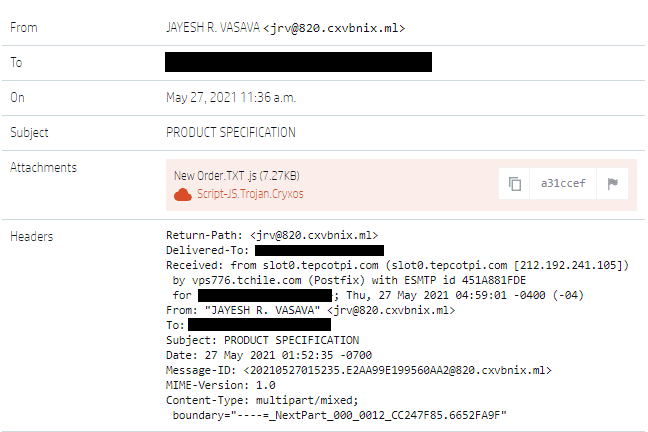
The attack starts off as a phishing email containing a malicious attachment. The JavaScript disguises itself as a text file, which supposedly contains information about a certain order.
All the malware needs to run is for the user to double-click the attached file. You can check the image that HP provided in their report below:
According to HP, the loader will write a VBScript file to the %TEMP% folder. After that, it downloads the malware (RAT) payload.
RATDispenser – Hide & Conquer
HP used one of the most reliable virus detectors on the internet – Virus Total. Unfortunately, the malware’s obfuscation techniques allowed it to avoid detection 89% of the time.
According to the company:
“Although JavaScript is a less common malware file format than Microsoft Office documents and archives, in many cases it is more poorly detected. From our set of 155 RATDispenser samples, 77 were available on VirusTotal which allowed us to analyze their detection rates. Using each sample’s earliest scan result, on average the RATDispenser samples were only detected by 11% of available anti-virus engines, or eight engines in absolute numbers.”
As we mentioned, RATDispenser distributed 8 different malware families. These include all of the following:
- STRRAT
- WSHRAT
- AdWind
- Formbook
- Remcos
- Panda Stealer
- GuLoader
- Ratty
For example, the Formbook malware family acts as a keylogger and information stealer. However, RATDispenser does not focus on distributing this type of malware.
In fact, the most frequently observed malware families were STRRAT and WSHRAT, which have typical RAT capabilities such as remote access, credential stealing, and keylogging features.
Phishing Enhanced – Download, Launch, and Dispense RATs
Distributing remote access Trojans (RATs) and information stealers through phishing emails has become a very popular way for attackers to target new victims.
HP found this vulnerability and gave us everything we need to know about it. Now, it’s up to you to learn more in order to avoid such a predicament in the future.
Whenever you receive an email, make sure it comes from a legit source. If there’s even a 1% doubt, never click on any link. Visit the source manually. Stay safe.