Avast Privacy Invasion: Revealed & Proven
With so many online threats nowadays, it’s very difficult to trust your computer programs. However, we never thought that this line of thinking would apply to antivirus software, let alone one of the best out there, Avast. This free antivirus software is used by millions of people around the world on their PCs and mobiles. But what if the best is treating your personal information in the worst way ever? Is the world’s popular Anti-virus a Spyware now? Let’s find out.

Avast – Antivirus to Anti-Privacy Software
It’s not as surprising as everyone thinks. We all know that free products aren’t actually for free, especially when they’re software. Despite being the perfect shield to online threats, it has become a threat itself to its users’ privacy.
Apparently, one of the world’s favorite antiviruses is selling highly sensitive web browsing data to many of the world’s biggest companies. All this data is analyzed by Jumpshot, a company that’s 65%-owned by Avast.
Jumpshot is all about analytics, and if you’re using Avast, rest assured the company knows everything you like, purchase, or show interest in.
As we mentioned, Avast and Jumpshot are selling your data to big companies such as Google, Microsoft, Yelp, McKinsey, Pepsi, Condé Nast, Home Depot, Intuit, and many more.
In fact, here’s an example of what Jumpshot knows when it comes to consumers visiting major “walled garden” marketplaces: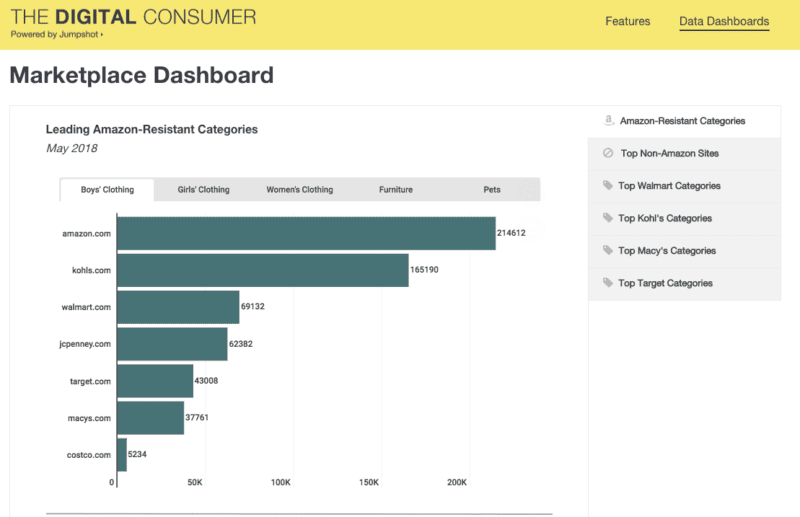
It’s all in the open now. Avast says that it has more than 435 million active users per month, and Jumpshot admits that it has collected data from over 100 million devices.
Jumpshot’s website offers weekly updates and dashboards displaying consumer data relating to big companies. For example, it provides graphs on Amazon’s Total Traffic and Conversions, Top 20 Product Purchases, Leading Amazon-Resistant Categories, and even top beauty product purchases made online.
If they’re not collecting your data, how else are they getting the information needed for such analysis?
They’re Transparent After All
We’re not saying that collecting user data is a good thing, but in Avast’s defense, they already told us that they’d do such a thing. First, let’s focus on its privacy policy. The following is some of the data Avast gets a hold of if you use their product:
- Billing Data includes your name, email address, credit card number, and in certain circumstances, your billing address and your phone number. In most circumstances, our products and services are purchased from a trusted third-party service provider, reseller, or app store. In those circumstances, your Billing Data is processed by the relevant third-party, and we only receive a subset of this data to keep proper business records.
- Account Data includes your name, address, email address, phone number, photo, date of birth, gender, and interests, and this data is used to register an account with Avast.
- Product Data includes two sub-categories:
- Device Data includes information about the operating system; hardware; city/country of the device; error logs; browser; network; applications running on the device, including the Avast products; and
- Service Data includes information about Avast product usage and events.
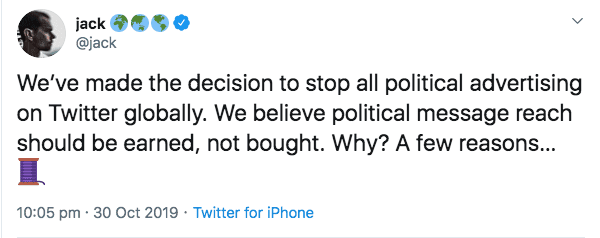
The App Warns Us
They keep reminding their users, whether old or new, that their product will collect data if operated with. Avast COO Ondřej Vlček explains:
“We are aware that some users don’t want any data – no matter how generic and depersonalized it is – to be used in market analysis. This is why we clearly state during the installation of our products what information we collect and what we do with it, and offer our users the ability to opt-out from having that data collected.”
Technically that’s true as the moment you install their PC version of the Anti-virus, a warning message pops up before you can carry on with the installation process.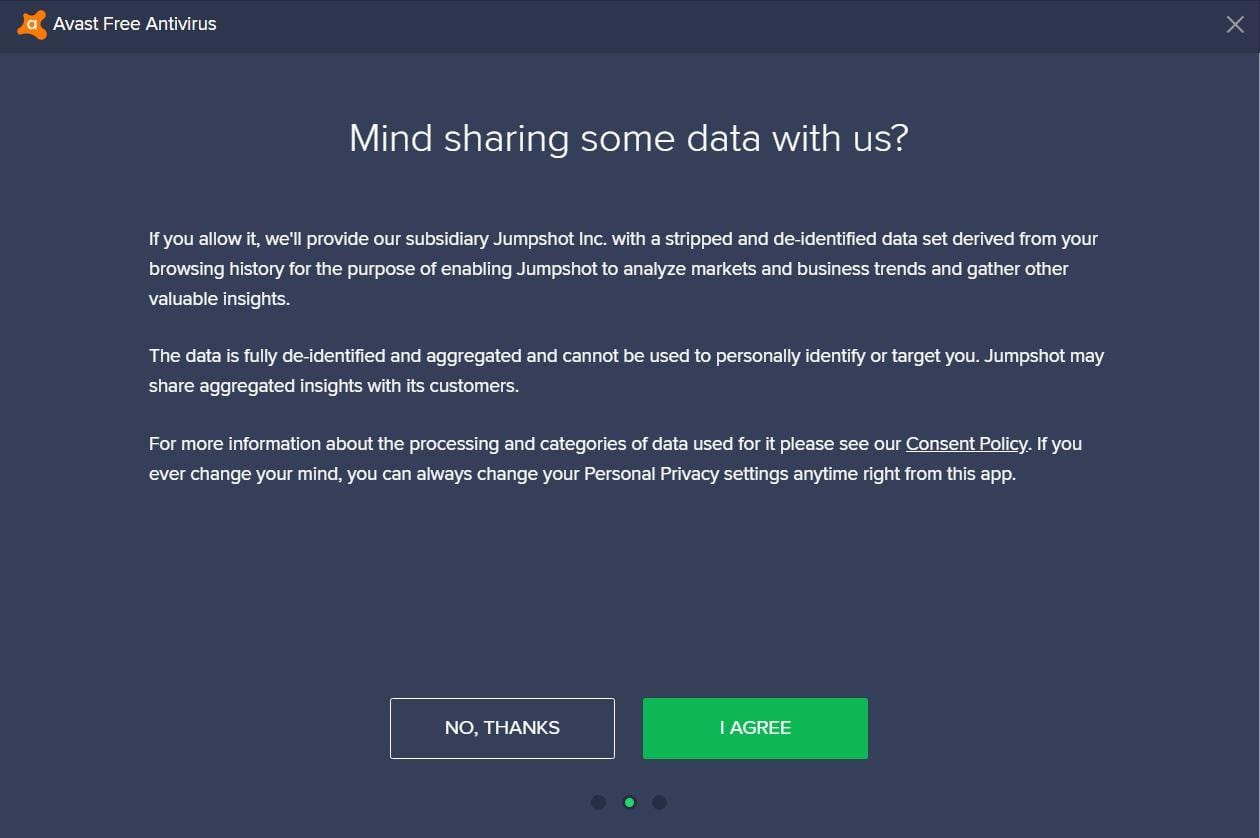
So, it’s basically up to you to determine whether you allow them access to your data or not. They’re being fully transparent. Now that Jumpshot is mentioned in the “Notice” above, let’s see what the data is de-identified and aggregated.
What Avast Claims – De-Identification Process
At first, we used the words may and might while judging Avast’s actions. But now, it’s all out in the open. The antivirus company addressed its users on the issue, justifying the practice as completely harmless to users’ identity.
According to Avast:
“The data is fully de-identified and aggregated and cannot be used to personally identify or target you.”
They claim to strip the customers’ web histories of personal details before handing them off. As a result, user privacy is conserved, the company gets paid, and online marketers get chunks of consumer data to help them sell more products.
A Home Depot spokesperson stated that:
“We sometimes use information from third-party providers to help improve our business, products, and services. We require these providers to have the appropriate rights to share this information with us. In this case, we receive anonymized audience data, which cannot be used to identify individual customers.”
While it might seem like a win-win situation, personal data is still shared, which always raises concerns among internet users. Even the CEO of the company, Ondřej Vlček, took it upon himself to address the issue and shed some light on the matter:
De-Identification – In-Depth
The first process is called stripping, where all PII parameter values (Personally Identifiable Information) are removed from the raw data. Jumpshot applies an algorithm to determine which parameters have PII values and which don’t.
The parameters that lack PII values are whitelisted, and their values are kept. However, the ones that don’t get whitelisted are stripped in the process and get overwritten by the word “REMOVED.”
With a shopping site like Amazon, the URL before stripping contains some PII:
https://www.amazon.com/gp/buy/addressselect/handlers/edit-address.html?ie=UTF8&addressID=jirptvmsnlp&addressIdToBeDeleted=&enableDeliveryPreferences=1&from=&isBillingAddress=&numberOfDistinctItems=1&showBackBar=0&skipFooter=0&skipHeader=0&hasWorkingJavascript=1
The algorithm automatically replaces the PII with the word REMOVED in order to protect our users’ privacy, like this:
https://www.amazon.com/gp/buy/addressselect/handlers/edit-address.html?ie=UTF8&addressID=REMOVED&addressIdToBeDeleted=&enableDeliveryPreferences=1&from=&isBillingAddress=&numberOfDistinctItems=1&showBackBar=0&skipFooter=0&skipHeader=0&hasWorkingJavascript=1
Next, there’s aggregation. This ensures that no reverse engineering is possible on the aggregated data – there’s nothing that can lead back to a specific user. Ondřej Vlček further explained:
“To further protect our users‘ privacy, we only accept websites where we can observe at least 20 users. This ensures that no reverse engineering is possible on the aggregated data – there’s nothing that can lead back to a specific user. All aggregated data is then stored in an RDBMS (currently PostgreSQL) database on a per-domain and keyword basis.”
De-Identification – De-Anonymized
As we already covered, Jumpshot sells the data they collect from Avast to big brands and e-commerce providers to help them learn what consumers and where consumers are buying products.
Whether it’s from Google, Amazon, an ad from a news article, or a post on Instagram, rest assured, they know. While they do claim that none of the data is linked to a person’s name, email, or IP address, there’s one thing to consider.
De-identification itself is harmless, but with a bit of work, anyone can de-anonymize the data. Each user history is assigned to an identifier; it’s what we call a Device ID.
It’s a collection of numbers and letters that help identify every individual’s mobile, tablet, or PC in the world. In case you’re not aware of the term, take a look below:
- On iOS, the Device ID goes by the name of ‘Identity For Advertisers’ (IDFA, or IFA for short).
- On Android, you can find the Device ID in your Settings – Google – Ads – Advertisement ID.
In general, a user’s timestamp information, device IDs, along with the collected URLs, can be easily analyzed to determine his/her true identity.
You Can Be Identified
We’re going to give you a random example of what a single click would like in the image below:
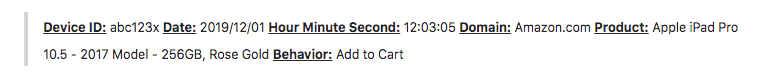
Now, it might not look like much or harmful at all, but the device ID has a huge role in tracking your true identity. Theoretically, no one can pin the device ID to a specific user, but the company/website they’re purchasing an item from definitely can.
We’re taking Amazon as an example (As the image shows above). Amazon can determine exactly which Amazon user purchased an iPad Pro at the exact time and date.
As a result, the anonymous device ID you see is a person (a known user). Now, whatever Jumpshot has on this device ID’s activity from other e-commerce purchases is no longer anonymous.
It’s a simple cross-referencing. Some data here and sone there, combine them together, and you get an identified user. Gunes Acar, a privacy researcher who studies online tracking, said the following:
“Most of the threats posed by de-anonymization—where you are identifying people—comes from the ability to merge the information with other data. Maybe the (Jumpshot) data itself is not identifying people. Maybe it’s just a list of hashed user IDs and some URLs. But it can always be combined with other data from other marketers, other advertisers, who can basically arrive at the real identity.”
See, de-identification might not even work if any online entity sets its eyes on the users’ data. This can be a problem later on if you keep on using Avast products.
The “All Click Feed”
Jumpshot offers a variety of products the collect browser data in so many different ways. For example, it has a product that focuses on searches people are making. If you’re using Google, for instance, the product collects the keywords you use and the results you clicked on.
We have to mention another product, which tracks each video users are viewing on Youtube, Facebook, and other social media platforms. Moreover, there are others that analyze select e-commerce domains to help marketers get an idea about how users are reaching them.
As for the All Click Feed, this occurred back in 2018 with Omnicom Media Group. The company signed a contract with Jumpshot to gain every click Jumpshot has collected from Avast users.
If the Jumpshot claims to anonymize their customer’s data, this is exactly where they get caught with their hands in the cookie jar. The company should sell the data without device IDs. That’s to protect against the triangulation Personally Identifiable Information.
However, as part of the deal with Omnicom, Jumpshot is, unfortunately, delivering the information along with device IDs that belong to each click.
Omnicom doesn’t own a major internet platform, but they do acquire the Jumpshot data through a subsidiary that goes by the name of Annalect.
Well, Jumpshot does respect user privacy, as they mentioned before. But respect aside, money speaks in such situations. Omnicom now has access to daily click-stream data on 14 markets, including the UK, US, India, and more. In return, Jumpshot is getting $6.5 million.
It’s Way Bigger Than We Think
Harvesting user information for targeted ads by big companies is well-known, but the fact that these targeted ads have a much bigger purpose, that’s where question marks start to rise.
Ads have turned the internet into a surveillance nightmare. Any social media platform collects your data and targets you with ads related to what you show interest in.
Other forced targeted ads involve politics. This can be very destructive as no one knows where the ads are coming from or how legit they are. That’s why, around two months ago during the elections in the UK, Google and Facebook were urged to suspend political ads until from their platforms until after the voting is done.
Twitter also moved against targeted ads. You see, just like Avast, other platforms also sell your data for revenue. But during such elections, some of them have to step up.
Well, Jack Dorsey did and posted a Tweet announcing the political ads ban:
“We’ve made the decision to stop all political advertising on Twitter globally. We believe political message reach should be earned, not bought.”.
Google also banned political advertising two weeks prior to the polling day. In the Israeli and Canadian elections, political ads were blocked outright for the duration of the election period as well. It’s what we call Election Silence.
That’s just half of it. Those harmless polls you like to participate in are also part of a bigger plan. When it comes to the internet, statistics matter. These polls can be very effective in elections. They can help completely turn the tides in someone’s favor as they may target those in the middle who haven’t made a decision yet.
Can You Prevent Data Collection?
Well, yes it’s possible if you know your way around it. As a start, we’re going to be covering the application. After that, we’ll head over to how you can stop data tracking while using the Avast browser extension. Here’s what you need to do:
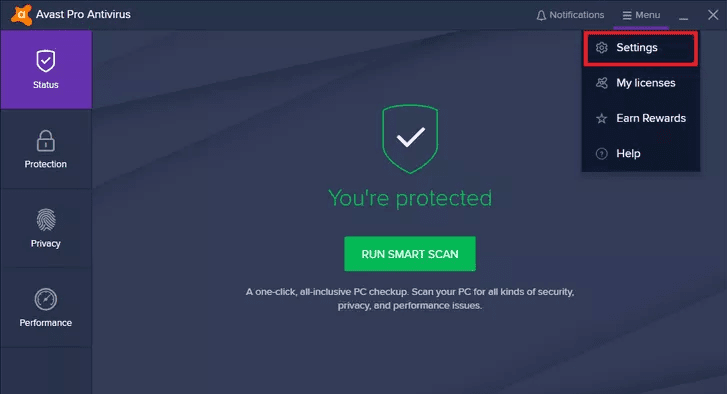
- First, activate the Avast Anti-Virus app and head over to Settings.
- In the Settings Page, navigate to General followed by Privacy.
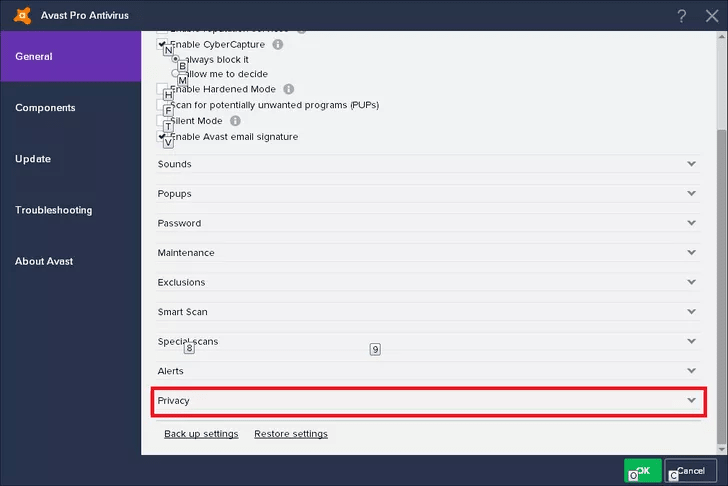
- Next, at the end of the page, you’ll find everything that’s related to data collection.
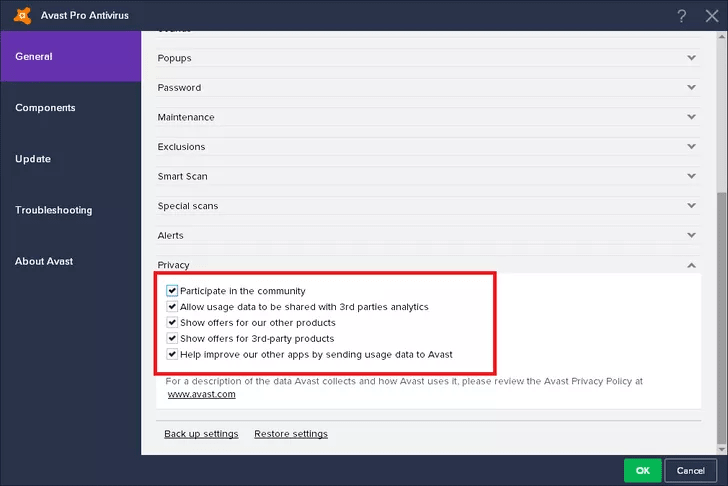
- Untick everything so that Avast doesn’t collect your data and store them.
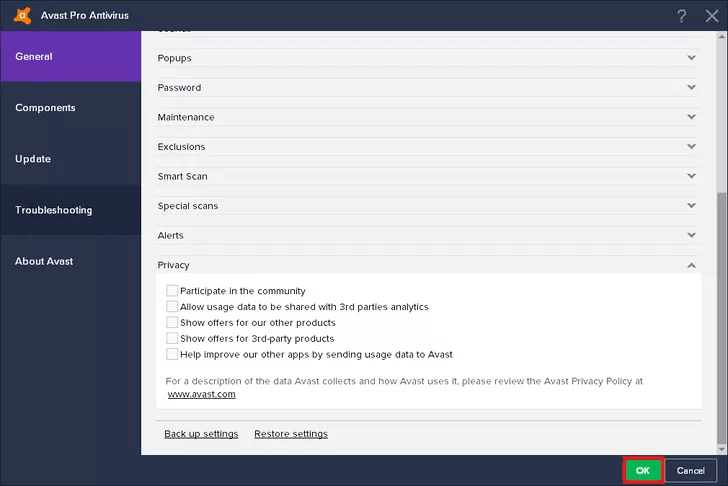
- Finally, you now can use Avast to protect your self without jeopardizing your privacy.
You now know how to deactivate data collection while using the Avast application. Next, we’ll cover how to turn it off if you’re operating with an extension. Here’s how you do it:
- On your browser, which is most probably Chrome, click on the Avast icon on the top right of your screen.
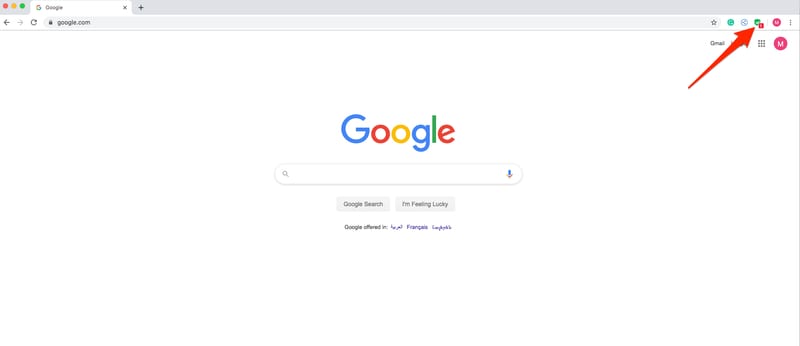
- Tap on the Gear Icon to navigate to the Settings Section.
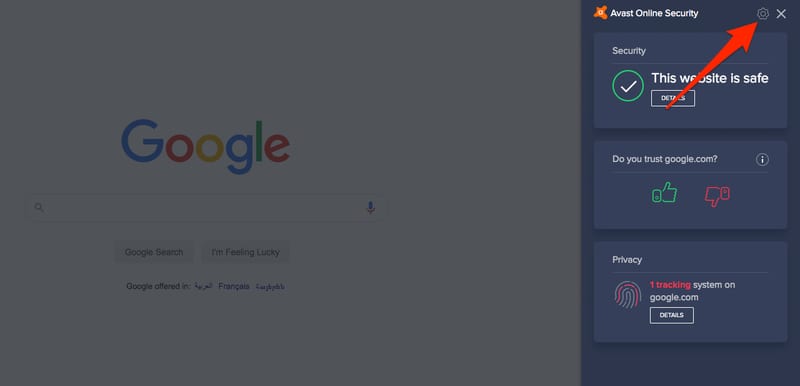
- Scroll down until you see the Privacy Section.
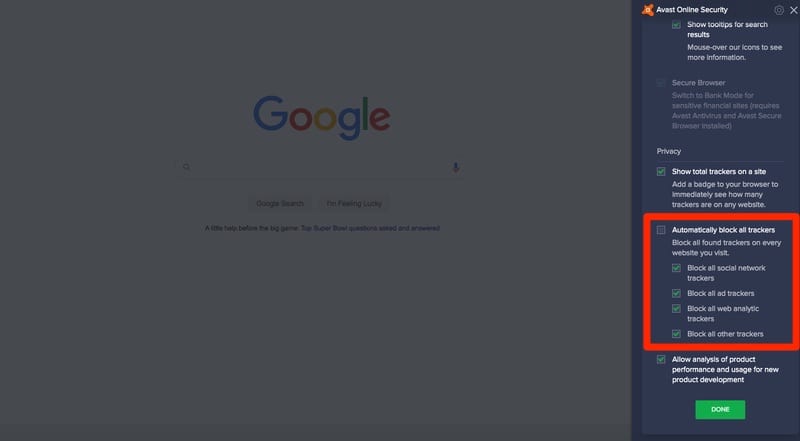
- Now, either untick them all or enable “Automatically Block All Trackers.”

- Avast will no longer store your data as you now completely turned off that option.
It is very easy to follow the steps above and deactivate the Tracking Option. However, if you want to guarantee your privacy and avoid Avast’s data collection, simply uninstall the entire software.
Avast-owned Companies To Keep a Keen Eye On
Now that you know that your privacy is at risk, we should shed some light on Avast’s subsidiary companies. If Avast collects your data, rest assured that the following do so as well:
- AVG Technologies
- Piriform
- Jumpshot
- HideMyAss!
One of the best ways to secure your data and hide your identity online is by using a Virtual Private Network. Despite offering such service on its own, Avast also owns HideMyAss, one of the popular VPNs in the industry.
We’ve already reviewed HideMyAss. But we’re going to give you a brief explanation about it while we’re discussing privacy. If you think HideMyAss is any better than Avast’s technology, well, think again.
The provider has some major privacy issues, where data collecting and sharing has become a habit to this service. A while ago, a hacker named Cody Kretsinger was arrested by the FBI for hacking into Sony Pictures’ website.
This shows that HideMyAss does keep logs of their users’ browsing activities despite stating otherwise. If you read the review we made on HideMyAss, you’ll find everything you need when it comes to privacy invasion.
Well, as they say, “The Apple Doesn’t Fall Far From the Tree.”
Is Avast Shutting Down the Subsidiary?
Now that people know Avast is harvesting browsing data and selling it to advertisers, the company stated that it would be shutting down the subsidiary responsible for it all.
Avast CEO Ondrej Vlcek says that the company is terminating its Jumpshot subsidiary’s data collection and operations “with immediate effect.” Here’s his full statement:
“Protecting people is Avast’s top priority and must be embedded in everything we do in our business and in our products. Anything to the contrary is unacceptable,” Vlcek wrote. “For these reasons, I – together with our board of directors – have decided to terminate the Jumpshot data collection and wind down Jumpshot’s operations, with immediate effect.”
We still don’t know whether this is taking effect immediately or not, but at least it’s a start. On the other hand, we have to think about all the data it has already collected. What happens now? Do they delete it or keep it for future use?
The company also does not mention any plans to transfer the company’s “hundreds” of affected employees. In other words, there might be hundreds losing their jobs very soon.
Avast Privacy Invasion – Final Thoughts
Avast is indeed one of the more popular and widely-used antiviruses in the world. However, while it’s enhancing your device’s security for free, it is siphoning all of your personal information.
Privacy matters and online targeted ads are changing the world. Now, you have everything you need to know about how Avast is collecting your data. You’ve also learned how you can avoid it. Act upon what you learned today and never jeopardize your privacy again, even if it’s for the sake of your security.