No More Data Encryption – BianLian Shifts to Pure Data Extortion
Ransomware operations are simple in terms of execution. Threat actors gain access to a system, install encryption payloads in their attacks and ask for a ransom. But when a decryptor is available for a certain ransomware family, the group behind it is forced to seek alternatives. In today’s case, we’re referring to BianLian ransomware.

Following Avast’s release of a BianLian decryptor a while ago, the group had no other way than to look for an alternative in their practices. They’ve resorted to data extortion instead of encrypting their victims’ files.
So, the question is: If BianLian is not encrypting data anymore, how are they asking for a ransom? Oh, they are, and here’s everything you need to know.
BianLian Ditches Encryption – Ransom Still in Place
When it comes to ransomware, the process has been the same since the beginning. Cybercriminals infiltrate their victims’ devices, encrypt their data, and ask for an amount of money in exchange for a decryption key.
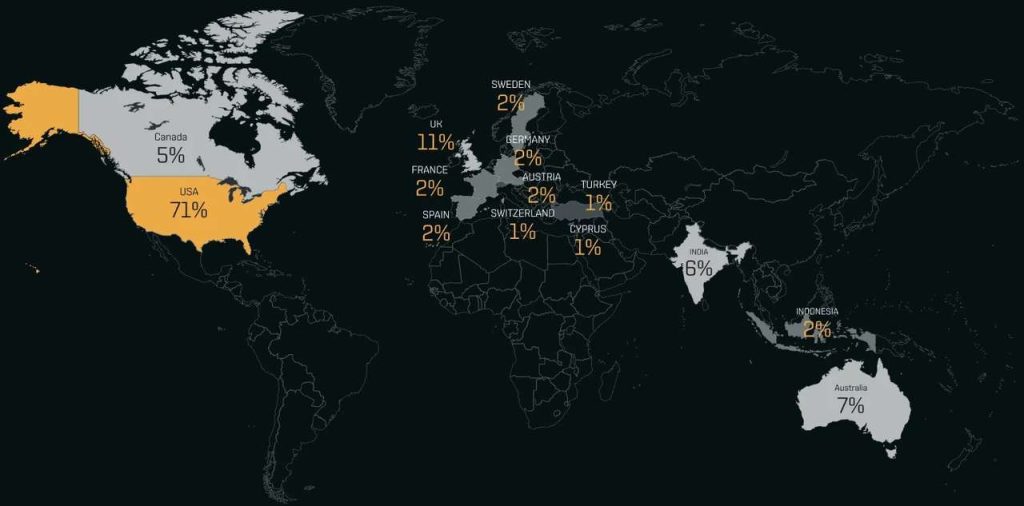
BianLian is one of the most notable ransomware families of all time. With over-the-top capabilities, this family terrorized big companies, especially those in the United States.
Companies weren’t the only targets. Even Android users suffered from BianLian’s activity as the malware itself found its way into Google Play Store through malicious applications with millions of downloads.
So far, nothing has changed until cybersecurity firms decided to take a stand and fight those malicious activities. BitDefender, the popular cybersecurity company, came up with a decryptor for the MortalKombat ransomware.
Avast, on the other hand, started this comeback with one of its own to battle Hades ransomware. However, Avast didn’t stop there, as it also came up with a decryptor for BianLian.
Now, since there’s a decryptor, one would think that the group behind the ransomware would call it quits. Well, that wasn’t the case with BianLian, as they decided to continue their operations but with a different attack mechanism.
Yes, BianLian has recently been spotted monetizing its breaches without encrypting the victim’s files. So, how do they ask for a ransom? Simple! The group’s strategy involves threatening to leak stolen data if they are not paid.
“The release of the tool appears to have brought about a shift in how BianLian attempts to monetize the successful compromise of a victim.
Rather than follow the typical double-extortion model of encrypting files and threatening to leak data, we have increasingly observed BianLian choosing to forgo encrypting victims’ data and instead focus on convincing victims to pay solely using an extortion demand in return for BianLian’s silence.
The group promises that after they are paid, they will not leak the stolen data or otherwise disclose the fact the victim organization has suffered a breach. BianLian offers these assurances based on the fact that their “business” depends on their reputation.”
Source: Redacted
Sometimes, to convince the victim to pay the ransom, BianLian shows the company what the data would do to it in terms of causing legal and regulatory issues. Clever approach, don’t you think?
BianLian Retaliates – Decryptor Deemed Useless
The threat actors behind BianLian have done their homework. To formulate strong arguments, they’re actually analyzing what legal risks the stolen data can pose when released to the public.
We don’t know if the group has abandoned the encryption tactic due to the presence of Avast’s decryptor, but based on recent incidents, it seems like they’re sticking to extortion for the time being.





