Facebook Messenger Phishing Scam – Outsmarted by a Fake Chatbot
We’ve all contacted some sort of customer support, be it via email or live chat. If our questions were simple, chatbots would step in to help before redirecting us to a live employee for further assistance. But what if a threat actor is impersonating the company’s support team chatbot? Well, that’s the new Facebook Messenger phishing scam.

Social media platforms have had their fair share of phishing attacks in the past year, especially those that involve a “Deactivation Warning.” A couple of months ago, Instagram users fell victim to a similar attack.
Now, it’s Facebook’s turn as the attackers are sending warning emails that lead to them stealing credentials for managers of Facebook pages. What is this campaign all about, and how do they pull it off? We’ve covered everything below.
A Facebook Messenger Scam – You Appeal, They Steal
Any reputable company should provide its users with several means of support, especially on social media platforms. It creates a page where customers can contact their support team directly through Facebook Messenger.
This is the ultimate opportunity for threat actors to strike as anyone could be tricked in this situation. The new phishing campaign sees attackers impersonating Facebook.
We discussed using the “Fear” factor in phishing attacks and that’s exactly what the attackers preying on. The victims receive an email stating that their Facebook page has violated Community Standards.
Not only that, but they also give them 48 hours to appeal the decision. Otherwise, the platform will delete the page (Fake claim of course).
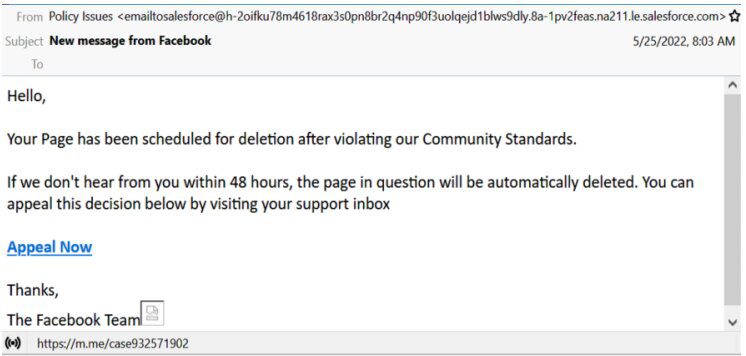
As with most phishing emails, a link is present, providing the target with some hope of saving their account. All they had to do is click on the “Appeal Now” button to access Facebook’s Support Center.
The moment the tap on the link, a Messenger conversation appears and a chatbot will initiate a conversation. Of course, the chatbot is a threat actor impersonating a Facebook customer support agent.

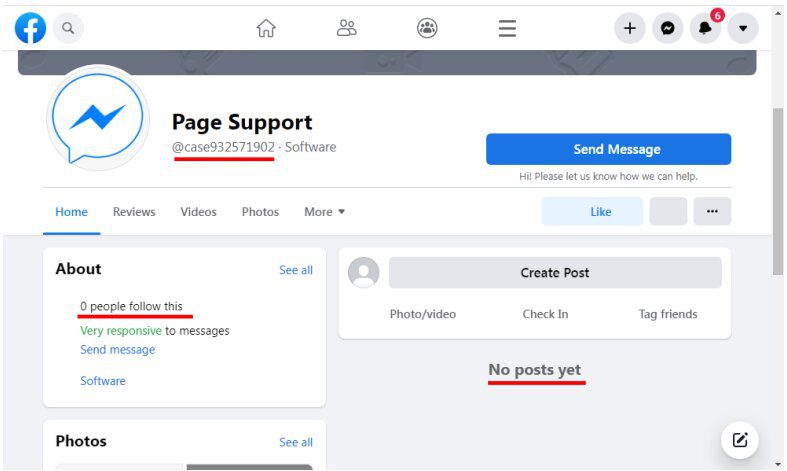
The Facebook page associated with this is pretty standard. What a keen eye might see is that the page does state that it’s very responsive.
This can be very beneficial for the attacker as such a statement will attract the victim. However, if they looked even closer, they’ll notice that the page has no followers, indicating that something is definitely off.
Now, back to what happens in the chat box. The Appeal Now button will redirect the user to a fake website that looks like Facebook Support Inbox. If you look closely at the domain, it’s not associated with Facebook.
According to TrustWave – the firm that discovered the campaign, the case numbers in both the page and the chat box don’t match. However, fear plays a huge role the users won’t notice that in their panicking state.
Final Step: Give Us Your Credentials
The final step, well, you know what happens now. The users are prompted to enter their information. To stop the account deletion process, the victims must submit their email address, full name, page name, and phone number.
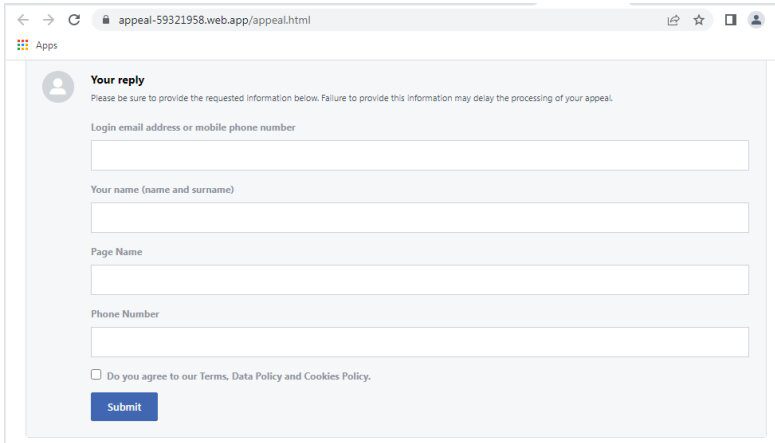
And here is where we say: “A single click can cause a lot of damage.” Entering the information is the start of the problem, but pressing submit reveals more.
Once clicked, the fake page asks for the user’s password. The attacker then receives all the information via a POST request.
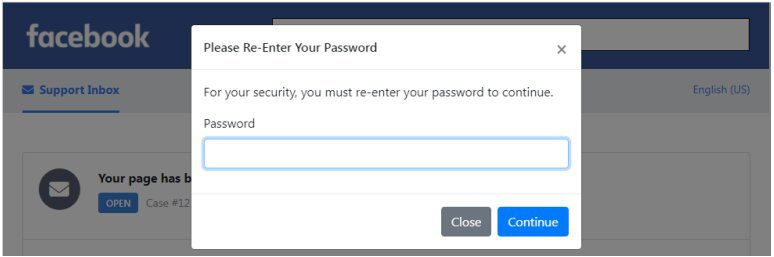
In the information field, the targets had to provide their phone number. As a result, the final step requires them to enter the OTP they received via SMS on a fake 2FA page.
Any OTP could work, but the user doesn’t know that. It’s just there to give the authenticity illusion, nothing more.
Facebook Messenger Phishing Attack – Chatbot? More like TrickBot
Such phishing campaigns are on the rise, and they’re not focusing on one social media platform only. In fact, Instagram, Twitter, TikTok, and any other platform are susceptible to such attacks.
To avoid this, never follow a link sent via email. If there’s something of importance, you can visit the official source manually.
It’s Facebook eventually, so opening the official app and contacting the company directly won’t be a hassle. Avoid this scam, avoid drastic damage.





