Android vs. VPN: Always-on VPN Rendered Useless
Virtual Private Networks exist to elevate users’ online security and privacy. However, regardless of how reputable the VPN is, if the operating system itself is sabotaging its job, risks are bound to be present. Well, that’s exactly the case now with Android OS.

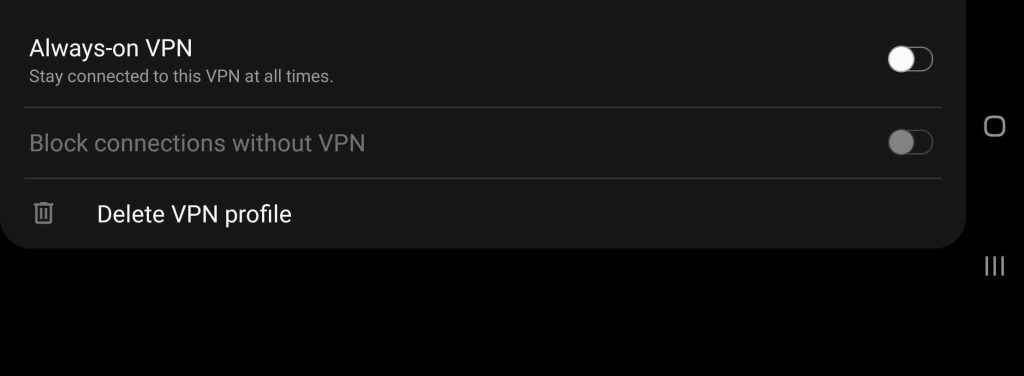
Yes, Android is indeed leaking data every time we connect to a WiFi Network. And yes, even when we’ve enabled “Block connections without VPN or “Always-on VPN” feature, the leak is happening.
This “Leaking feature” is a design choice, and it’s definitely built into the Android operating system. No Android user was aware of this fact until Mullvad VPN discovered it during one of its regular security audits. Here’s what we know so far.
An Android Flaw? We Think Not
When it comes to evaluating VPNs, a lot of features should be taken into consideration. Be it speed, security, privacy, or pricing; the process is quite delicate.
Simply put, we’ve reviewed Mullvad VPN in the past, and, to be honest, it’s not that reliable. Now the question is: Why trust what it has to say about this leak?
It’s easy! Every VPN hires a specific firm to perform a security audit. In other words, it’s the audit we trust. The problem starts with some sort of inaccurate description of the “VPN Lockdown” features – that’s why most users don’t know about it.
Most VPN providers offer a built-in kill switch; it’s the industry standard now. However, this option is also provided by the Android device itself under “Network & Internet.”
This feature terminates any network connection when the internet goes down or the VPN suddenly crashes. It does that to prevent any of your data from leaking back to your ISP’s servers, revealing your actual IP address and browsing history.
Well, apparently this is not the case on Android, as the operating system was found leaking data despite having the “Block connections without VPN/Always-on VPN” setting on.
Apparently, Android needs to leak some of our data to identify captive portals that must be checked before the user logs in, i.e., it’s bound to happen.
Mullvad contacted Google to publicize the issue as well as ask it to add the option to disable connectivity checks:
“This is a feature request for adding the option to disable connectivity checks while “Block connections without VPN” (from now on lockdown) is enabled for a VPN app.”
We have to stand by Mullvad VPN since the users’ privacy is at risk. According to the security audit, the leaks include information such as source IP addresses, DNS lookups, HTTPS traffic, and likely also NTP traffic. In other words, there’s too much on the line.
Did Google Comply? Not Quite!
Mullvad did send Google an eye-opener and a request to add an extra function. However, Google did not take this lightly and responded with an instant title: Status: Won’t Fix (Intended Behavior).
The response also states that the feature is working as intended. Here’s what the rest of the statement includes:
“As for disabling connectivity checks :
The VPN might be actually relying on the result of these connectivity checks (they are available through public APIs).
The VPN may be a split tunnel, letting part of the traffic over the underlying network, or only affect a given set of apps. In both these cases, the connectivity checks are still necessary for smooth operation of all the legitimate traffic that doesn’t go over the VPN.
The connectivity checks are far from the only thing exempted from the VPN ; privileged apps can also bypass the VPN and this is necessary for their operation in many cases. An example is IWLAN, or tethering traffic.
It’s unclear to us what specific privacy impact is meant. The connectivity checks reveal there is an Android device at this address, which is plenty clear from the L2 connection and from the traffic going over the VPN anyway.”
Mullvad replied to this with yet another suggestion stating that if Google doesn’t want to add anything or fix this, it should at least update the documentation.
That way, it’ll clearly indicate that ‘Connectivity Checks’ would not be protected by the “Block connections without VPN/Always-on VPN” feature.
Mullvad Steps Up – The Importance of Security Audits
A VPN’s first and main job is to secure a user’s data from being intercepted by third parties. With Google’s feature that leaks this information, the VPN won’t be able to do its job.
Connectivity checks? Users operate with VPNs, particularly when they connect to public networks. In our opinion, a disabling function should be added; otherwise, the insignificant data Google was talking about will be the least of our problems.





