A Huge Mangatoon Data Breach – Millions of Accounts Exposed
Comic books are fun but are sometimes hard to obtain. However, thanks to online platforms like Mangatoon, fans are provided with the convenience of accessing them online. Unfortunately, the fun can quickly turn into a disaster if a security breach occurs and that’s exactly what happened with Mangatoon.

The last couple of months saw several data breaches, including what might be the biggest one in China’s history. Well, the bigger the platform/company is, the more impactful the breach is.
Mangatoon is a very popular online comic book provider and the breach got it good. More than 23 million accounts have been exposed and users went into a frenzy. What happened? How is Mangatoon handling this, if it is? Find out below.
Mangatoon Data Breach – A Big Pow! to their System
Manga fans are all over the world. In fact, Mangatoon’s application harnessed more than 10 million downloads on Google Play Store alone.
Imagine if we combine that with iOS and all other third-party sources. That would give us a clear idea on how many Manga Otakus are there around the world.
Sadly, popular platforms and applications have become targets to cybercriminals as they can benefit a lot from them. A while ago, the most prolific messaging app, WhatsApp, was used in a phishing attack.
Now, what is probably the most famous Manga comic book platform suffered a breach, exposing more than 23 million user accounts in the process.
This week, Have I Been Pwned – the service that allows users to search across multiple data breaches to see if their email address or phone number has been compromised – added 23 million Mangatoon accounts to their platform. According to a post on their Twitter account:
“Mangatoon had 23M accounts breached in May. The breach exposed names, email addresses, genders, social media account identities, auth tokens from social logins, and salted MD5 password hashes.”
It doesn’t stop here. In the introduction, we asked: How is Mangatoon handling this? Well, apparently, and according to the HIBP owner, Troy Hunt, they’re not.
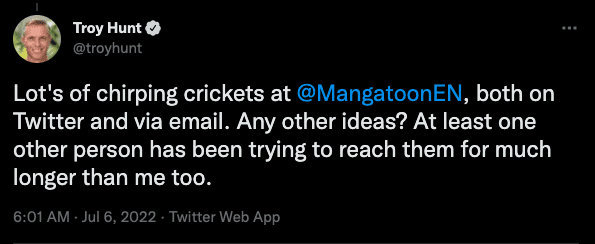
Hunt tried attempted to contact the company and inform them about the data breach. However, Mangatoon did not respond:
“Lot’s of chirping crickets at @MangatoonEN, both on Twitter and via email. Any other ideas? At least one other person has been trying to reach them for much longer than me too.”
As seen above, Mangatoon is not responding to anyone. However, concerned users can check if they were affected by searching for their email addresses on HIBP.
And the Hacker Is!
Despite not getting anything out of Mangatoon, we know who is behind the breach. The attack goes by the name of “pompompurin,” a well-known hacker who harvested the data from an Elasticsearch server that was using weak credentials.
Thanks to BleepingComputer, the firm that contacted the hacker, some light was shed on the matter. Here’s what pompompurin had to say:
“It was ES, they had credentials on it but it was just “password”, they changed the credentials after I emailed telling them but they never notified their customers and never replied.”
Aside from the statement, pompompurin shared some of the data with BleepingComputer’s representatives, which on their end, confirmed to be valid accounts on the Mangatoon platform.
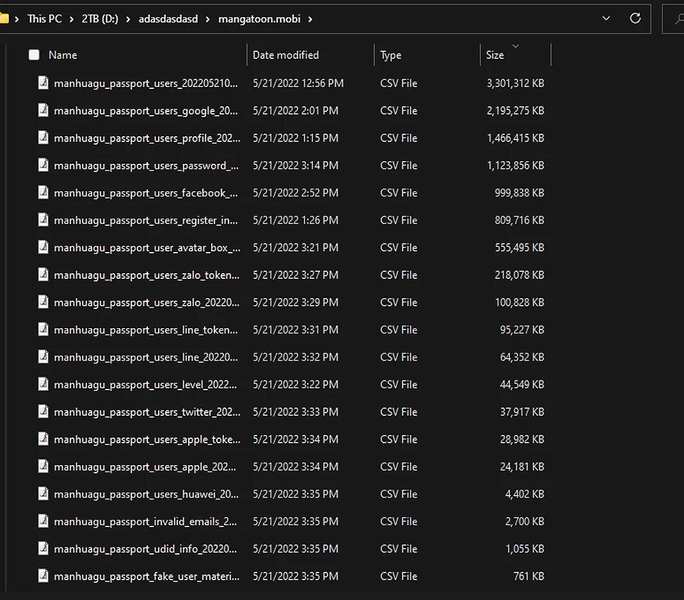
Now the question is: Will the hacker sell or leak the data? When asked by BleepingComputer, the attacker informed them that he will probably leak it at some point.
Mangatoon Breach – pompompurin Strikes
This is not the attacker’s first rodeo when it comes to high-profile breaches. pompompurin has previously targeted several victims, including ones using fake cyberattack emails through the FBI’s Law Enforcement Enterprise Portal (LEEP).
Data breaches are on the rise, and whether you’re an individual or a person who owns a country, you should always take proper precautions to protect yourself.