Why Password Protection is Superior to Fingerprint and Face Locks
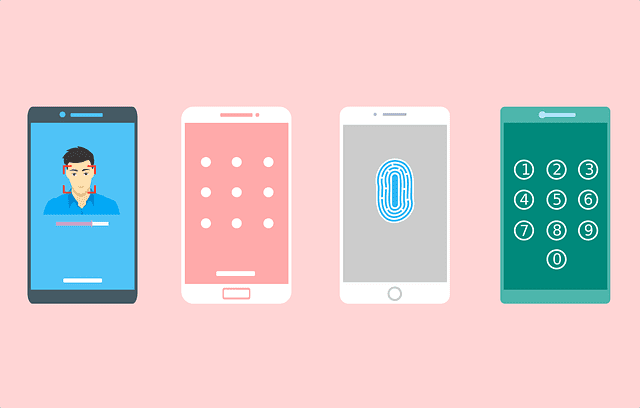
The fact is Password protection is the best way to secure your smartphone. Security technology is growing robust with each passing month. With a spate of new user protection technologies being offered on the latest cell phone devices, there is no shortage of options to choose from. The average user might believe that their phone is absolutely secure with these new facilities. However, as these features are being released to the masses, so are their breaches.
Why Password Protection is Superior to Fingerprint and Face Locks
The Introduction of Biometric Scanners
Now, the situation is such that even with the most sophisticated biometric scanners and data security systems, there is no guarantee of total safety. Moreover, since the utility of smartphones in our daily lives has grown by leaps and bounds, people are becoming increasingly concerned about their personal data use as well as investment records.
The truth is – fingerprint scanning is much easier than passwords and PINs. There’s no need to remember anything and you can just touch to unlock your phone. So yeah, fingerprint scanning is simpler, but which method is more secure?
About the Law
If you’re worried about the government gaining access to your personal information, using a biometric lock can be a bad choice. According to the Fifth Amendment, the police cannot force you to give up the PIN or password of your device. They can, however, ask you to unlock your phone with your fingerprint.
So if you want to keep your data out of the reach of the government (for example, if you’re planning to join a peaceful protest), make sure you keep your phone locked by a password and not by fingerprints.
About hacking
These days, iPhone is offering a dual security level check on through the Touch ID Fingerprint sensor and the PIN code. While the latter is certainly is a robust system with little chance of direct breaching, the former can be hacked rather easily and that too with not even the most sophisticated systems.
Here’s how it works. German security researchers working for the government were able to expose a security flaw of certain people by simply creating fingerprint forgeries using only a bunch of HD photographs. When you make that peace sign in front of the camera, you are actually exposing your fingerprint and any hacker with the time, energy, and dedication might be able to bypass your phone security solely based on this!
Now, whether the face recognition about to be unveiled by Apple late this year is going to be a step forward towards greater security or not is in question. However, it is clear that anyone with the right materials and tools can certainly gain a degree of access to all your personal information stored on your phone.
Taking biometrics a Step further
Another security feature widely touted by Android companies and available in the most recent models like the Samsung Galaxy S8 is the iris lock. This feature works by scanning the retina of the user and ensuring that none other than the user themselves can unlock the phone. This may seem like an effective measure to keep hackers at bay. But you must know that a breach has already been perpetrated and is available to anyone willing to make the effort to get to your personal data. This is how it was done.
Certain designated employees from the Chaos Computer Lab were able to access sensitive data on experiment phones using photos of the iris of the users. The photos were HD and were taken at close range, which allowed a near perfect or at least, practically useful copy of the retina to be created.
To further accentuate the shape of the eye, a simple lens was placed on top of the laser printed picture. This method was able to con the phone into thinking the iris belongs to the original user and thus allowed the hackers to get through.
So if you are thinking that your iris cannot be forged in a lab setting by a group of dedicated hackers, then you are sorely mistaken. Though these breaches have been successful only in lab settings with high-end tools, it will not be too difficult for an experienced and versatile hacker to gain access to your personal information.
When speaking of voice recognition, hacking becomes even easier. A hacker just needs to mimic your voice and speech pattern for a sample of your voice. This can be accomplished by something as simple as a call to your phone which you answer. More capable hackers can get even better samples by simply intercepting any of your phone calls routed through unsecured channels.
What is the Alternative?
When high-tech fails you, the best way out is to go back to the basics. The PIN lock has been an integral part of smartphone security ever since smartphones themselves were invented. This security feature has lasted the test of time for a very good reason. It is practically impossible to break into any device that provides a pin security feature. While early 3 to 4 digit numbers were somewhat easier to bypass, the modern 6 digit variant is not so easy to fool.
Also, when combined with other security features, as we have detailed in this article, you are provided with a comprehensive two or even 3 step security protocol that is very hard to breach even with the most advanced hacking tools at work. Therefore, to think that your phone’s security is truly impregnable just because it has high-end biometric sensors would be a naïve assumption.
What is really required is a robust security measure that makes full use of the PIN security protocol along with any number of biometric recognition facilities. This way, you can effectively make your phone as safe as modern technology can allow and feel safe about storing your most sensitive information on it.





