Google Play in the Spotlight… Again! Xenomorph Malware Resurfaces
It seems like Google Play Store’s security measures are not enough anymore. Cybercriminals are apparently finding various ways to infiltrate the store’s library, injecting malicious applications every now and then. A while ago, it was the Sharkbot malware. Now, it’s Xenomorph.

Xenomorph is one dangerous malware that can easily harvest banking credentials from the infected device. And that’s exactly what the threat actors behind it are after in this campaign.
Simply put, malicious applications masqueraded as popular lifestyle apps. In other words, the attackers knew how to spread the malware. We’ve discussed everything about this incident in the following article.
Xenomorph Strikes – A Malicious LifeStyle
Google Play Store doesn’t seem to have the ability to keep up with what cybercriminals can do now. They’ve developed advanced techniques to infiltrate the Android store, and they’re obviously succeeding.
In 2022, more than 8 campaigns were reported when it came to Google Play Store distributing malicious applications. Yes, Sharkbot was one of many.
The Xenomorph banking malware is the newest guest to Play Store’s library. This trojan can do a lot of damage as seen in past incidents.
Back in February, Xenomorph targeted around 56 European banks with one task at hand – Siphoning sensitive information from the devices of their customers.
So, how does it operate? Well, the malware needs access, so its first step would be asking the victim to enable access permission.
Once the user allows access, Xenomorph injects itself as a device admin and prevents users from disabling Device Admin. In other words, it cannot be uninstalled.
With it in place, it takes control over legit banking apps on the device to trick users into entering their usernames and passwords (Credentials).
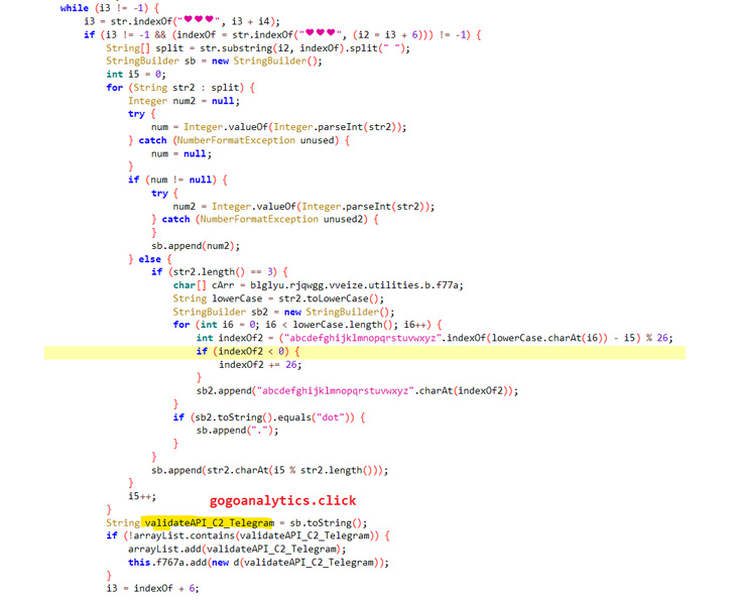
Unfortunately, it doesn’t stop here as the malware can also intercept SMS messages. That means it can steal OTP messages and multi-factor authentication requests.
According to Zscaler ThreatLabz researchers Himanshu Sharma and Viral Gandhi:
“Xenomorph is a trojan that steals credentials from banking applications on users’ devices. It is also capable of intercepting users’ SMS messages and notifications, enabling it to steal one-time passwords and multi-factor authentication requests.”
As mentioned, the main task is to harvest banking information. That’s easily done by presenting fake login screens atop legitimate bank apps. It’s a very convincing trick – it occurs without the user suspecting anything.
Play Store Infiltrated – Morphing at Its Best
Xenomorph is one of many malware families that are targeting Android users via the Play Store platform. Unfortunately, the store’s security measures can’t seem to keep up with the new techniques the threat actors are coming up with.
This campaign follows several others, and the damage has been done. Google Play Store removed the two applications included in this campaign: Todo: Day manager and 経費キーパー.
Anyone who installed these apps is advised to remove them immediately. Also, run a quick scan using a reputable anti-virus tool so that you can get rid of any remaining infections.





