Adobe ColdFusion Vulnerability: CVE-2023-26360 Exploited in the Wild
2023 has seen its fair share of security vulnerabilities so far. The biggest companies in the world are disclosing flaws and releasing updates to prevent them from being exploited in the wild. Unfortunately, not all companies can fix the problem in time, which is exactly the case with Adobe ColdFusion.

Usually, when a flaw is present within a company’s systems, it directly discloses it. However, this time around, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) is the one that issued a warning after signs of wild exploitations.
According to the report, the vulnerability is dubbed CVE-2023-26360, and it allows threat actors to achieve arbitrary code execution. What do we know about it? Make sure to give this article a quick read.
A New Vulnerability – Adobe ColdFusion Edition
When we speak of vulnerabilities, every single company is concerned. Whether it’s a software company such as Sophos, or a tech giant like Apple, system flaws are inevitable.
Speaking of inevitable, who can forget the infamous Log4Shell vulnerability that terrorized tech companies around the world? It’s still lurking around, waiting to be exploited once more.
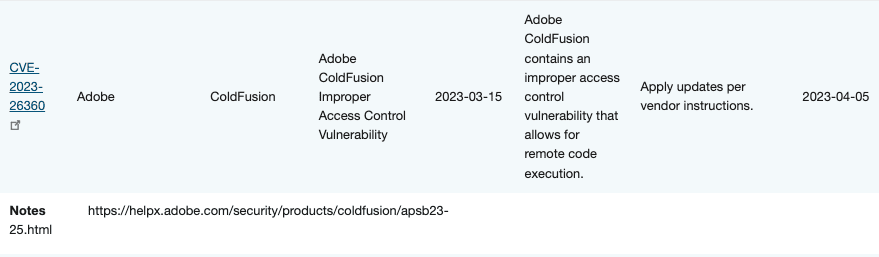
Now, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a new vulnerability to its catalog. This flaw is found within Adobe ColdFusion, which can lead to full arbitrary code execution.
“Adobe ColdFusion contains an improper access control vulnerability that allows for remote code execution.”
Source: CISA
Basically, not all versions of ColdFusion are impacted by the vulnerability. Only ColdFusion 2018 (Update 15 and earlier) and 2021 (Update 5 and earlier) are at risk.
This vulnerability doesn’t stop here. It also affects 2016 and ColdFusion 11 installations. However, since these releases are not supported by the company anymore (Reached end-of-life “EoL”), there’s no risk at all.
Now, since CISA addressed it, so did Adobe. The software company addressed this flaw in versions Update 16 and Update 6, respectively, on March 14th, 2023.
“Adobe has released security updates for ColdFusion versions 2021 and 2018. These updates resolve critical and important vulnerabilities that could lead to arbitrary code execution and memory leak.
Adobe is aware that CVE-2023-26360 has been exploited in the wild in very limited attacks targeting Adobe ColdFusion.“
Source: Adobe
Since the updates are out, Federal Civilian Executive Branch (FCEB) agencies should implement them as soon as possible to prevent any possible threats.
Vulnerability Fixed – Update Immediately
The researcher that discovered the flaw (Charlie Arehart) is urging everyone using ColdFusion to apply the newly released update.
Charlie insisted that the flaw is a “grave” issue that can easily lead to “arbitrary code execution” and “arbitrary file system read.”
Make sure you update ColdFusion now. It’s very important to do so. Otherwise, your systems and sensitive information will be at risk.