DoNot Definitely Does – Google Play Has Spyware
2023 didn’t kick off as expected for Android users. In fact, these past couple of months saw various campaigns targeting Android operators, especially through their official app store – Google Play. This time is not different, as, unfortunately, Google Play was seen hosting apps embedded with Spyware thanks to DoNot APT.

Google Play Store has had its fair share of malware infiltration recently. The AhRat malware was freely roaming around the store, infecting thousands of devices.
Now, state-sponsored threat actors are using three applications, including a VPN, to collect intelligence from infected devices in Asia.
What are the apps in question? How does the malware operate? We’ve discussed everything below.
Google Play – New Campaign, Same Old Predicament!
Threat actors will target anyone if they’re benefiting from the process. The more high-profile an organization/individual is, the more valuable they become.
Usually, these cybercriminals use phishing campaigns that lure the victims into downloading malicious files from untrusted sources. That’s why we always recommend using official stores.
However, as it may seem, even those can have a hard time dealing with capable threat actors. Google Play Store has had a rough 2022, and it seems like it’s continuing in 2023.
We can’t forget that one incident where cybercriminals spread malware through Minecraft clones on Google Play Store. Now, they’re using popular tools that can easily fool anyone.
In this campaign, three apps are spreading the spyware, including one “Chat” app and a VPN client. VPNs are meant to protect us, and this time around, they’re used to spy on us.
The VPN app goes by the name of Ikhfaa, which is Arabic for “Becoming Invisible.” Unfortunately, that’s definitely not what it does, as in the background, the app is collecting more information than a normal VPN would.
These apps ask for risky permissions, such as access to the user’s contact list (READ_CONTACTS) and precise location data (ACCESS_FINE_LOCATION).
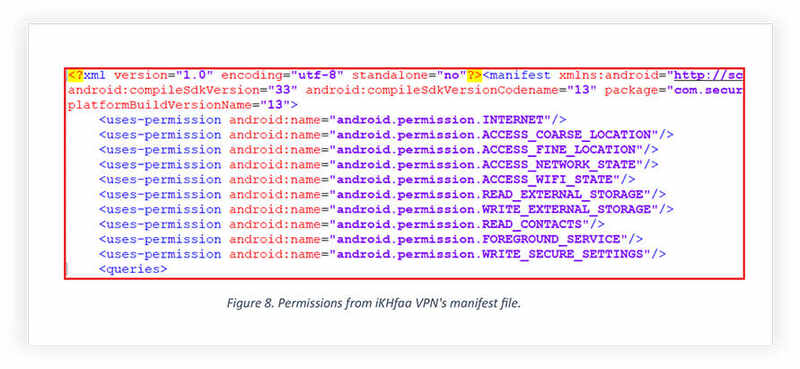
Once granted, they can exfiltrate this information to the threat actor. Here’s how these two privileges can affect the infected victims:
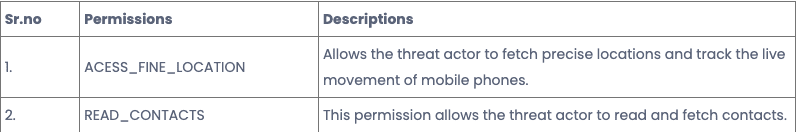
Apparently, the location permission allows the app to access the precise location of the compromised victim only if the GPS is ON. If not, it’ll just fetch the last location it can get its grip on.
According to Cyfirma’s report, there’s medium confidence about who’s behind this entire operation. The cybersecurity firm is linking it to the Indian hacking group “DoNot,” also tracked as APT-C-35.
Apparently, this particular group was seen around 5 years ago, targeting high-profile organizations in Southeast Asia.
Another Google Play Campaign – DoNot Install These Apps
When it comes to Virtual Private Networks, we always recommend premium services for various reasons. One of them is that free VPNs tend to collect sensitive information that can compromise a user’s privacy.
Some free VPNs function normally, but the one in question now definitely doesn’t. Not to mention that Chat applications should always provide some sort of encryption and ensure that the users’ privacy comes first.
With these permissions, everything is at risk. The threat actors used to operate with phishing attacks. However, the dropped this tactic in favor of spear messaging attacks via WhatsApp and Telegram.
Direct messages redirect users to Google Play Store, adding an extra layer of legitimacy to the campaign. Watch out and be extra careful when downloading any application, even on Google Play Store.





