AhRat Malware Emerges – Google Play Used Maliciously… Again!
Google Play Store is the best and safest way to download content if you’re operating an Android device. However, lately, the app library hasn’t been having the best days, as cybercriminals have managed to infiltrate it and inject malicious apps repeatedly. Unfortunately, it happened again, but this time, it was the AhRat malware.

This is not Play Store’s first rodeo in the malware department. It’s been seen hosting malware-injected apps for quite some time now. It hasn’t been a week yet since the last incident.
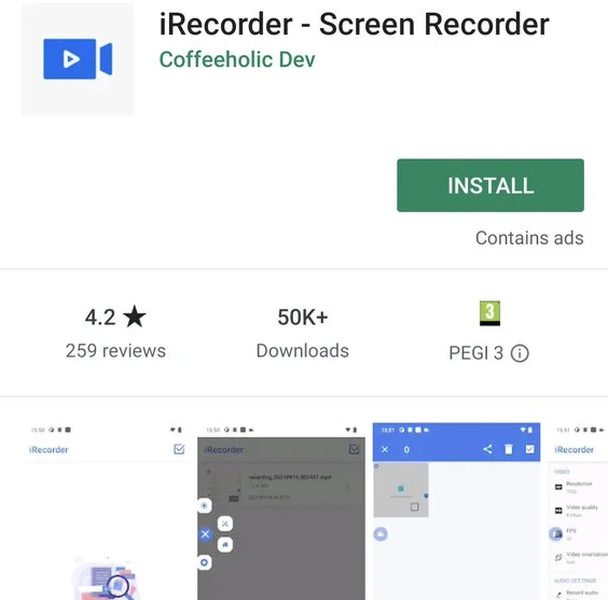
This time around, it comes in the form of iRecorder – an Android screen recording app with tens of thousands of installs. What is this app? How can AhRat impact an infected device? Here’s what we know.
AhRat Malware – A New Google Play Store Breach
Malware is literally everywhere. Users always fall victim to online scams and end up installing malicious programs on their devices.
That’s why it’s always recommended to download content from a trusted source. However, that’s not always the case, as we’ve seen what trusted sources have been witnessing lately.
Google Play had a rough 2022 and early 2023. In fact, in April alone, the Android library suffered multiple infiltration attempts via malware-injected apps.
One of these incidents saw cybercriminals creating Minecraft clones infected with adware and spreading them through the Android store. The clones had millions of downloads, which showed how big the campaign was.
Now, with the incident at hand, the malware infiltration comes in the form of a screen recorder called iRecorder. It has amassed over 50,000 installations on the Google Play Store.
The AhRAT malware is not new in terms of functionality. It’s designed based on an open-source Android RAT known as AhMyth. According to ESET malware researcher Lukas Stefanko:
“Previously, the open-source AhMyth was employed by Transparent Tribe, also known as APT36, a cyberespionage group known for its extensive use of social engineering techniques and targeting government and military organizations in South Asia.”
Once it takes root within a device, it can perform all sorts of malicious practices, including:
- Track infected devices’ location.
- Steal call logs.
- Harvest contacts and text messages.
- Send SMS messages.
- Take pictures.
- Record background audio.
While 50K+ downloads don’t seem like a big deal compared to other campaigns, with such capabilities, the malware can do a lot of damage.
Using tools such as this one is popular among users. However, nowadays, each Android device has its own screen recorder. You don’t have to download any of these.
Google Steps In – App Removed
No matter how secure Google is, such incidents are bound to happen. Cybercriminals have elevated their techniques to even fool the almighty Google.
However, once the Play Store figures out what apps are injected with malware, it should immediately remove them. And that’s exactly what happened with iRecorder.
Aside from removing the app, there’s Google Play Protect, which warns users of identified malicious apps on Android devices. Watch out and stay safe.





