BlackByte Strikes Again – BYOVD at Its Best
With the discontinuation of the Conti group, a lot of cybercriminals are trying to make a name for themselves. However, with names like BlackByte, this is not the case. The group is an offshoot of Conti and it has struck again with a sophisticated BYOVD attack.
The infamous group is exploiting a flaw in a legitimate Windows driver to bypass security solutions to execute their latest BYOVD (Bring your own Vulnerable Driver) attack.
In recent years, this mechanism or practice has been increasingly co-opted by nation-state threat groups. Now, BlackByte is at it again and we’re here to discuss everything.
A BlackByte Attack – Security Solutions Begone
BlackByte has been around for quite some time now targeting big companies and names all around the world. Apparently, the group is carrying Conti’s mantle as it’s performing practices the discontinued faction was known for.
BYOVD is a very sophisticated form of attack in which threat actors abuse vulnerabilities in legitimate, signed drivers. Once they’re in, they can easily achieve kernel-mode exploitation and gain full control of compromised machines.
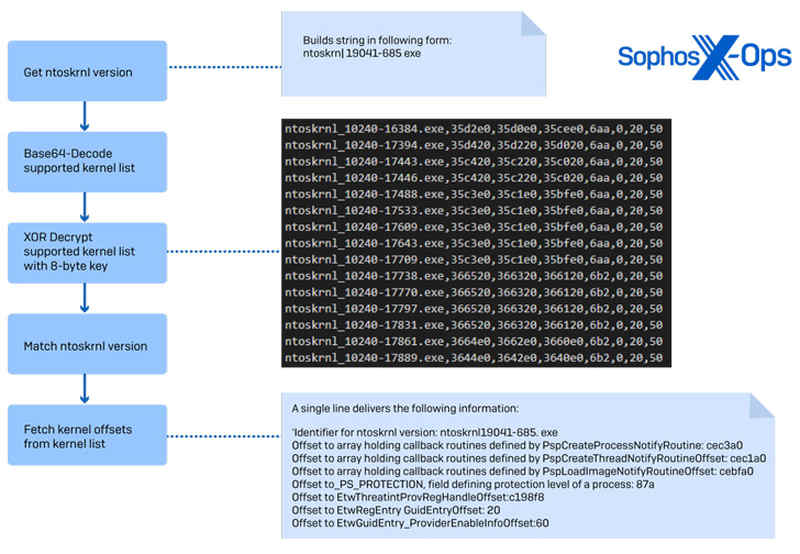
In this particular attack, BlackByte leveraged a flaw in a legitimate Windows driver that allowed them to bypass security solutions. According to Sophos threat researcher Andreas Klopsch:
“We found a sophisticated technique to bypass security products by abusing a known vulnerability in the legitimate vulnerable driver RTCore64.sys.
The evasion technique supports disabling a whopping list of over 1,000 drivers on which security products rely to provide protection.”
But wait, there’s more. The cybersecurity firm also shared what vulnerability the ransomware group is exploiting in this attack:
“RTCore64.sys and RTCore32.sys are drivers used by Micro-Star’s MSI AfterBurner 4.6.2.15658, a widely used graphics card overclocking utility that gives extended control over graphic cards on the system.
CVE-2019-16098 allows an authenticated user to read and write to arbitrary memory, which could be exploited for privilege escalation, code execution under high privileges, or information disclosure.”
As we mentioned, such attacks are pretty common among big names in the cybercrime world. We’re referring to the likes of Slingshot, InvisiMole, and APT28.
However, the scariest name among them is none other than the Lazarus Group. These threat actors have been busy lately, targeting victims with fake crypto job opportunities.
BYOVD Technique – The New BlackByte Mechanism
Aside from RobinHood and AvosLocker, BlackByte is the latest ransomware family to embrace the BYOVD method.
In other words, we can clearly state that cybercriminals are elevating their malicious practices. They’re targeting big companies and with these techniques, they’ll have high success rates.
Threat actors are preying on vulnerabilities every day. Once they exploit them, they can easily gain full control over the infected device.
Whenever there’s a vulnerability, the manufacturer issues certain updates with possible fixes. To avoid such predicaments, make sure to update your software to the latest patch.
Not only that but always approach anything with complete caution. Never click on links or submit private information on random platforms. Stay safe.





