A New WhatsApp Scam – Call Forwarding for Full Account Access
Targetting users’ WhatsApp accounts and gaining access to personal messages and contact lists is not a new trend for hackers. Several malicious campaigns targeted WhatsApp in the past. However, none of them were as innovative as to use a new trick involving Call Forwarding.

Threat actors are always finding new ways to infiltrate their victims’ devices. Now, with call forwarding to different numbers and the WhatsApp OTP option, hacking a WhatsApp account has become easier.
So, how can these hackers hijack a victim’s WhatsApp account and gain access to it? What are the users doing wrong to help the threat actors out with their malicious activities? Find out in the following article.
Call Forwarding? More Like Forwarding Access
WhatsApp had some vulnerabilities in the past, and apparently, threat actors are giving it everything they got to exploit more in the present.
The process is quite difficult, even for the most experienced hackers out there. However, there are individuals with the right skills, so they can manage to overcome these obstacles.
According to research, the attackers must first learn what the victim’s phone number is. Once that is out the way, they have to do some social engineering.
Social interactions are a huge part of this malicious campaign, so if the hacker cannot initiate a convincing conversation, the end result won’t be as he/she had hoped.
Rahul Sasi, the founder, and CEO of digital risk protection company CloudSEK stated everything related to this attack, including the method used to hack the WhatsApp account.
Give Us Your WhatsApp Account… Willingly!
The first step, as Rahul stated, should be convincing the victim to call a number that starts with a specific Man-Machine Interface (MMI) code. It is the code the mobile carrier set up to enable call forwarding.
Such codes begin with either a star (*) or a hash (#), which can be easily found as all major mobile network operators support them. Here’s what Rahul had to say:
“First, you receive a call from the attacker who will convince you to make a call to the following number **67* or *405*. Within a few minutes, your WhatsApp would be logged out, and the attackers would get complete control of your account”
Now, if the attacker managed to trick the user into forwarding calls to their number, the malicious magic starts.
The attacker will be able to start a WhatsApp registration process on their device. To make things easier, they choose the option to receive an OTP through a voice call. 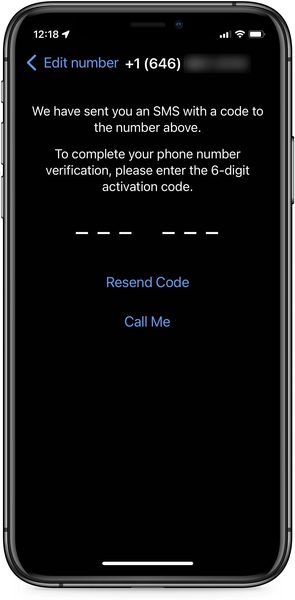
This trick is definitely believable and non-tech-savvy individuals will easily fall for it. The victim receives a call with the OTP, he/she enters it on their device, and the hacker takes over.
There will be warning signs along the way, and the user has to be suspicious. Why must they activate call forwarding? Why is there a warning on the screen that doesn’t go away until the user confirms it? Make sure to be vigilant all the time.
WhatsApp Call Forwarding Attack – Trust No One
As we always advise our readers, never trust anyone, especially if the practice is suspicious. If they have good social skills, they’ll try their best to convince you to do their bidding.
This alone should be an indication of a phishing scam as WhatsApp doesn’t do that. To protect yourself from such attacks, make sure you’re always vigilant when it comes to sharing sensitive data.
Not only that but also make sure that you have enabled two-factor authentication protection in WhatsApp. With this feature, you can protect your device from malicious actors as the PIN is only sent to you via text whenever a new login occurs.





