The Ultimate Disguise – Fake ExpressVPN Clone, Very Real RedLine Malware
Virtual Private Networks represent the perfect tools to protect your online security and privacy. If a VPN has a reputable name in the industry, it can be used as a disguise to perform various phishing practices. Unfortunately, this is recently the case as the number 1 VPN in the world, ExpressVPN, is being used to spread none other than the infamous RedLine Malware.

We’ve seen RedLine do its malicious work in previous attacks throughout the years. However, masquerading as one of the most popular VPNs in a campaign is a first.
ExpressVPN reflects ultimate legitimacy, which promises high success rates at the end of this malicious attack. How are the cybercriminals pulling it off? What can RedLine do once it takes root? Here’s everything you need to know.
Redline InfoStealer – Brand Impersonation at Its Best
Masquerading as a well-known brand is not a new tactic in phishing campaigns. In fact, if cyber criminals want the job done, they’ll have to add a dash of legitimacy to it, and that’s the perfect way to do so.
A couple of months ago, WhatsApp, the most popular social media platform was in the spotlight as threat actors utilized its Voice Message feature to spread the information-stealing malware JS/Kryptic.
From social media and all the way to cybersecurity, this new phishing campaign is as tricky as any other. This time around, the threat actors are taking advantage of one of the top VPNs in the world, ExpressVPN.
They’re using the brand’s popularity to trick people into downloading fake installers containing Redline, a widely distributed information stealer. Yeah, this malware is very capable – Just check what damage it did with 2K Games and Valorant.
It all starts with a fake page as the threat actors used typosquatting domains made to appear close to ExpressVPN’s actual domain. You can check what the fake ExpressVPN website looks like below:
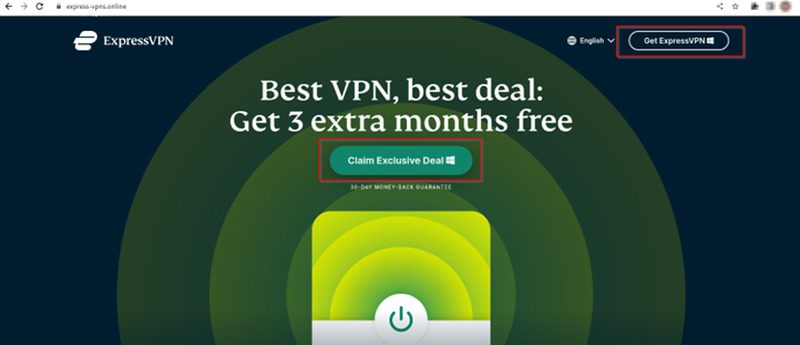
Just like what ExpressVPN’s offering, the phishing site is also offering a fake “3 extra months free” deal to the victim on Black Friday. This shows how dedicated the threat actors behind this are to making it as genuine as it can be.
Once the users click on the “Claim Exclusive Deal” button, the website will redirect them to the Discord app where the malicious ZIP file is available for download.
Now, RedLine will start to do its malicious practices in the background. The stealer payload begins to fetch the configuration settings from the Command and Control (C&C) server, allowing it to initiate the harvesting process from the victim’s system.
Imperfect Perfection
There are several ways a victim could end up visiting those pages. These include phishing emails, SEO attacks, online ads, and so much more.
According to Cyble Research & Intelligence Labs (CRIL), there are 6 identified phishing sites impersonating ExpressVPN to distribute this Windows malware:
- express-vpns[.]biz
- express-vpns[.]cloud
- express-vpns[.]fun
- express-vpns[.]online
- express-vpns[.]pro
- express-vpns[.]xyz
This is a well-crafted campaign and the resemblance is uncanny. However, if you look closely, you’ll be able to spot the differences.
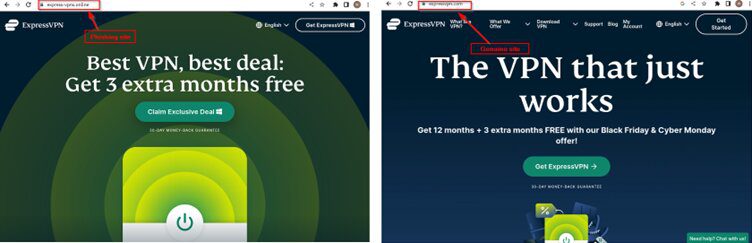
Avoiding such campaigns requires a keen eye for details. You can’t just run around downloading random stuff from any website.
You have to make sure it’s the official one, otherwise, you’ll end up a victim of cybercrime and who knows what malicious practices the threat actors will perform with the data they acquired.
RedLine Strikes Again – ExpressVPN? Not Quite!
ExpressVPN has had its moments when it comes to actual intentions, especially after being acquired by Kape Technologies. However, it’s proven its motives ever since.
As for the impersonation, that’s a huge deal. ExpressVPN is by far the most popular VPN service in the world. Can you imagine the damage RedLine can do with such a disguise?
All you have to do is Avoid downloading pirated software. Make sure to check the URL, and scan the page for anything that gives it up. Stay safe.





