How to Use VPN to Secure Your IoT Based Device
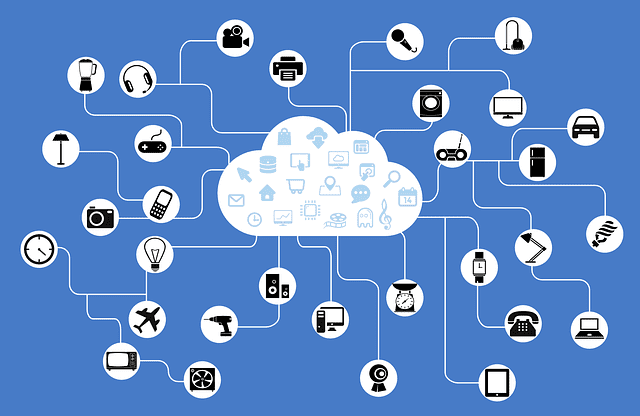
From smart houses, to automated driving, and to robots that can communicate with each other, the Internet of Things is a phenomenon whose capabilities we are only beginning to grasp. It allows for such a wide range for possibilities, some of which we are still yet to fully understand or even begin to explore. It’s probably safe to say that the next few years we’ll probably see a surge in innovations that have all been made possible thanks to this new concept, and you’ll also see a lot of innovations made around Internet security so that things actually go on the way they’re supposed to. For now however, we’ll have to rely on the very same form of security that we use to safeguard our online browsing, and that is VPN.
How to Use VPN to Secure Your IoT Based Device
What Is VPN?
A Virtual Private Network, also known as a VPN, is a type of technology that allows users to access the Internet through a secure channel, away from anyone hoping to eavesdrop, steal data, or hack through to your connection. If you’ve bought a subscription with a credible VPN service, and some third party network tries to intercept your connection, all they see is scrambled incomprehensible characters as a result of encryption. Using a VPN also allows you to hide your actual location, such that nobody will be able to discern where exactly you or your device may be.
Why Security for IoT Devices Makes Sense
Most of the IoT devices that are largely available to the public are known to have a very low level of computing power, owing to the fact that most of the operations to be performed don’t even require that much capacity. Implementing a VPN service between the IoT app server and the IoT device itself will ensure your device operates under complete protection, and prevent any instances of hacking to occur between your connection.
Security for IoT devices continues to be an area that not many have ventured into, and the evidence is seen for example when a group of university students were able to hack in to the traffic lighting system in Michigan and successfully change the colors displayed on the traffic light signal at will. If someone as skilled as the students from Michigan was able to access the lighting system as easily as they were, there’s a strong possibility that they could get to use their new found power to cause a lot of havoc. Using a VPN, alongside other security measures, helps safeguard against such occurrences, since the connections established would then become encrypted. In this case, a VPN would’ve helped lock down the camera to only communicate with recognized IP addresses, thereby preventing any form of outside access.
Using a VPN also allows you to retrieve data from your IoT device, without any limits as to which network protocol you can use. A perfect example of the application of this capability would be a mechanical engineering company that builds wind turbines, and sells them throughout the world. They decided to rely on built in SIM cards, so that whenever the turbines run into a problem, they’re able to remotely initiate a query and run tests to find out what the issue might be.
If they had implemented a VPN service, they would be able to ensure that nobody else has remote access to the turbines, and the data that’s retrieved is easily viewable from any workstation that’s connected to the VPN network.
The Protocols You Should Use For IoT Security
There are a number of well known VPN protocols that are very popular for use by customers, but the two protocols that we recommend for use with IoT devices are IPSec and OpenVPN.
IPSec
Internet Protocol Security (IPSec) allows you to set up a tunnel from a remote device, through to a central server, and is designed to facilitate secure, private communication over the internet through cryptographic services. It works best for large scale firms and businesses where many security layers and multiple peers are used. Using this protocol requires that you get a static IP address, and a lot of technical resources to get to implement. It is the best protocol to use especially if the data being transferred is of very sensitive nature.
OpenVPN
OpenVPN relies on the SSL/TLS security protocol where customers authenticate each other using a shared key. Using this protocol means OpenVPN users will have to connect to the OpenVPN server, and from then on, they will have complete access to the internet. This type of protocol is also favourable for users who have either static or dynamic IP addresses, and the software is now being provided by almost all the major VPN companies around. It’s great for SMEs that would like to enjoy premium security, and would also like to enjoy the flexibility of open source software.
Conclusion on Using a VPN To Secure Your IoT Based Device
Using an IoT device might not kill you, but it can certainly be used to jeopardize your privacy and security. There’s no safer bet when it comes to security for your IoT based device. A VPN service should allow you to ensure all your devices stay protected, and that you have a secure channel of communication between you and your device.





