Toll Fraud Malware – WiFi Disabled, Premium Subscriptions Enabled
Malware injection works in several ways, each more malicious than the other. Most of them are there to steal the victims’ information, but some go even further and subscribe to premium services without their consent. Unfortunately, the most known targets for such attacks are Android users who are yet again, victims of Toll fraud malware.

This type of malware is one of the most prevalent types of Android malware – and it continues to evolve. Apparently, a new campaign is spreading among Android devices and disabling their WiFi connection.
Finally, the malware fetches premium services and attempts to automatically subscribe to them – without the users’ consent or knowledge. So, what is Toll fraud, and what makes it so dangerous? Find out below.
Toll Fraud Malware – There’s a Joker in the Mix
In the past few months, malware injections and phishing attacks have reached new heights. In general, 2022 has seen a huge spike in cybercrime and this is considered very alarming.
Threat actors are developing new ways to target victims, steal their credentials, and even financially benefit from what they’ve collected.
Subscribing users to premium services after taking control of their devices is pretty common nowadays. They usually reach the victim through several means such as push notifications, promo pop-ups, and malvertising.
A couple of months ago, Android devices were targeted campaign that involves SMSFactory. The malicious application subscribes to premium services in the background without the user’s consent.
This time around, it’s not about credit cards or banks. The malware subscribes through the victims’ phone bills. According to Microsoft, the malware disables the phone’s WIFI access and forces the device to revert to its cellular network.
What’s worse is that some devices are very susceptible to the attack and don’t need a lot of force to infiltrate. If the victims are using Android 9 or below, the malware disables their WIFI by simply invoking the setWifiEnabled method of the WifiManager class. That’s it.
The Process
Microsoft explained everything in its full report and the process goes like this:
- Disable the Wi-Fi connection or wait for the user to switch to a mobile network
- Silently navigate to the subscription page
- Auto-click the subscription button
- Intercept the OTP (if applicable)
- Send the OTP to the service provider (if applicable)
- Cancel the SMS notifications (if applicable)
Aside from that, Microsoft discovered traces of the Joker malware that has constantly infiltrated Google’s Play Store for more than 5 years.
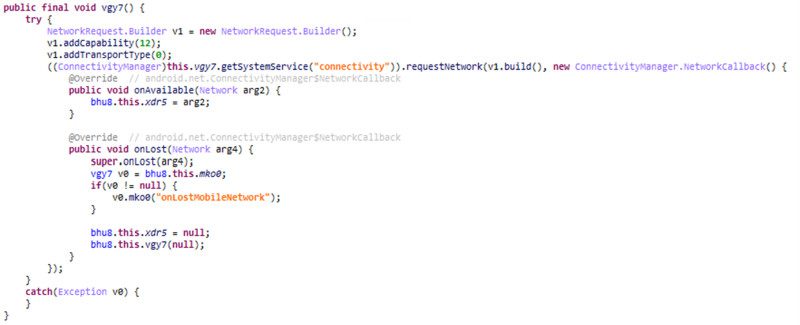
The malware can easily monitor the network status and the ‘networktype’ variable. This helps it to bind the process to a specific network and forces the device into ignoring ignore an available WiFi connection. As a result, it reverts back to the mobile operator’s network instead.
Toll Fraud Malware – A Very Costly Campaign
Microsft did find and report the campaign, but it also warns users of future attacks. When you want to download an app, we always recommend installing it only from the Google Play Store or other trusted sources.
Never go for unknown websites, they tend to be created by threat actors to infiltrate your devices. Also, never click on a link sent via email or text. If there’s something to be done, head over to the website manually. It would take a few more seconds, but you’ll be avoiding so much trouble.





