ChatGPT’s Popularity Utilized – Fake Apps Everywhere
ChatGPT launched in late 2022 and has harnessed huge popularity within a couple of months. However, in the world of cybersecurity, popularity also gains threat actors’ attention, and that’s exactly what it did recently.

Apparently, these cybercriminals are masquerading as OpenAI’s ChatGPT chatbot to distribute malware for Android and Windows devices. ChatGPT is not available through applications, but not everybody knows that.
Having a dedicated client grants convenience, and that’s what the threat actors are preying on. What is this campaign all about? How are these criminals utilizing this AI’s popularity? Find out in the following article.
ChatGPT – A Thin REDLINE Between Fake and Real
ChatGPT needs no introduction. In fact, this platform became the fastest-growing consumer application in modern history due to the fact that it amassed 100 million in terms of users within two months.
The service didn’t come without flaws, which forced many users to shift to alternatives. However, with constant updates, ChatGPT became a reliable ally for those who constantly surf the internet for information.
Due to the high demand the platform saw, the basic free access became overloaded. A lot of users had to join a waitlist to try out ChatGPT.
Now, OpenAI created a Premium Subscription plan that allows users to directly access the AI and benefit from extra privileges ($20/month):
- General access to ChatGPT, even during peak times
- Faster response times
- Priority access to new features and improvements
With this new upgrade, ChatGPT might even harness more popularity in the near future, and threat actors are well aware of that.
Despite being a huge platform, ChatGPT doesn’t have applications. But when users see that it does, they’ll definitely be tempted.
This is the threat actors’ strategy in this new campaign. The targets are users who operate Windows and Android. It kind of makes sense since those are more susceptible to malware injection than iOS and Mac users.
For Windows, the campaign kicks off with a fake page promoting ChatGPT’s new premium subscription and extra privileges, as reported by cybersecurity researcher Dominic Alvieri.
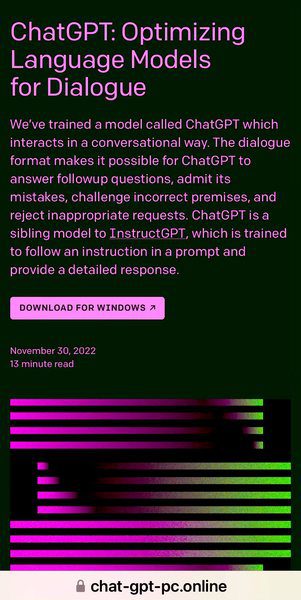
When the victims click on the “Download for Windows” button, the following popup will appear, prompting them to download a .rar file:
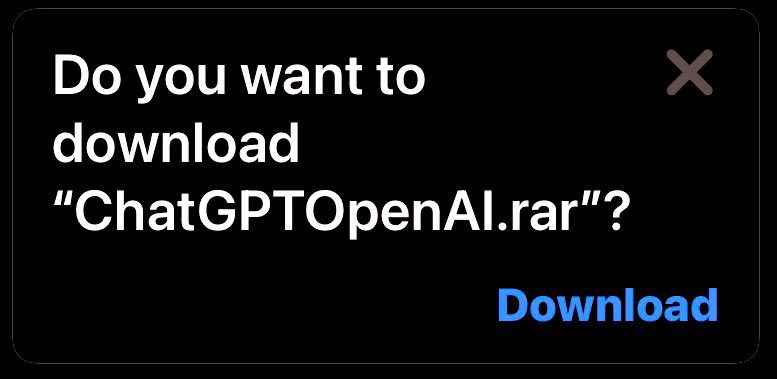
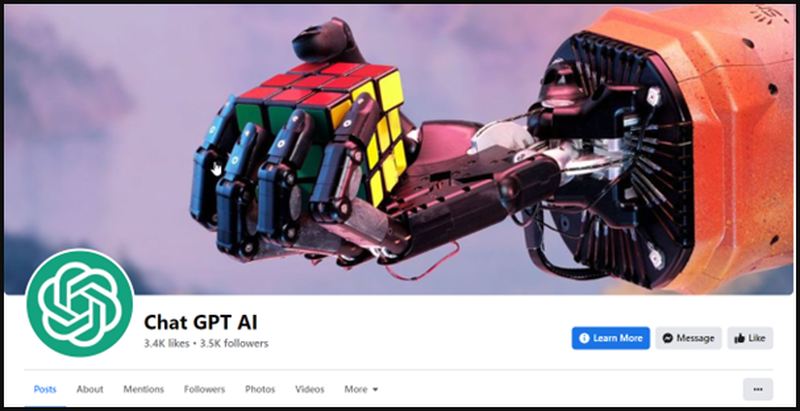
Once the file is executed on the device, the RedLine Info-Stealer sets in. How do they get to this fake page, you’re asking? Easy, a fake Facebook Page promoting ChatGPT.
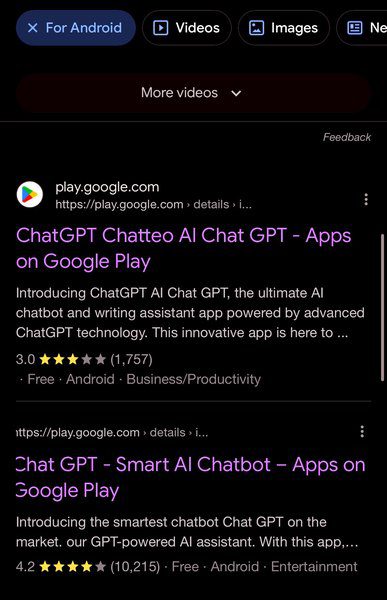
Unfortunately, it doesn’t end here. Dominic Alvieri also spotted the same campaign targeting Android users in the same way. What’s worse is that the fake applications are being distributed through Google Play Store – the source we all trust.
Researchers at Cyble further investigated what Alvieri discovered. They found out that more malicious activities are being practiced due to ChatGPT’s popularity. This includes stealing clipboard contents and installing further malware families such as Aurora.
Moreover, other threat actors are using a well-crafted card-stealing page at “pay.chatgptftw.com” – a fake payment portal to purchase ChatGPT Plus.
![Fake Payment Portal]](https://b626376.smushcdn.com/626376/wp-content/uploads/2023/02/Fake-Payment-Portal.jpg?lossy=1&strip=1&webp=1)
Based on Cyble’s research, more than 50 malicious applications using the ChatGPT’s icon and a similar name exist in the open with harmful intentions towards impacted users.
To avoid this entire predicament, you have to know that ChatGPT exists exclusively as an online-based tool at “chat.openai.com.” Any other website should be deemed fake instantly.
ChatGPT’s Popularity Backfires – A Perfect Malicious Opportunity
ChatGPT, so far, offers its services through web browsers. OpenAI did not launch any application for its AI platform.
If you come across applications with ChatGPT’s name, you should flag them as fakes attempting to scam or infect your devices with malware.
The Android campaign is over. Google Play Store removed all the applications from its library. ChatGPT is growing, and cybercriminals will take advantage of that. Be careful and trust no source other than OpenAI.





