Fake Volcano Eruption Alerts – SpyNote Takes Over Android
Threat actors have made a habit of utilizing current events to target individuals all over the world. Whether it’s war, conflict, or even the pandemic – these are all tools to be used for malicious practices. Those aside, cybercriminals are now using “Fake Volcano Eruption” alerts to inject Android devices with SpyNote malware.

The attack seems to be solely targeting users in Italy, pushing fake notifications that redirect users to a page where the info-stealing malware is hosted.
It’s a simple campaign that can do a lot of damage. And when we say that iOS devices are well-built in terms of security, we mean it (You’ll find out why later). So, what is this campaign all about?
A Malicious Eruption – SpyNote on the Move
Witnessing natural disasters such as earthquakes and volcano eruptions is hard enough on its own, let alone worrying about cyber threats that come with them.
Every time something happens around the world, threat actors make sure to utilize it in order to commit their malicious practices.
One perfect example of this is the time the coronavirus took over the globe. When the pandemic took us by surprise, threat actors started preying on people’s “Sense of urgency” in campaigns involving phishing emails.
That goes specifically to users who were looking for the first opportunity to get vaccinated. Now, since volcanos have been very active lately, cybercriminals saw a chance to erupt their own malicious activities.
The last volcano was Mount Etna, which erupted on Sunday (Aug. 13) after weeks of puffing out odd smoke rings.
In order to keep up with what’s going on, individuals in Italy rely on IT-alert – a legitimate public service operated by the Italian government.
Unfortunately, the threat actors are using fake versions of the service to deliver SpyNote malware.
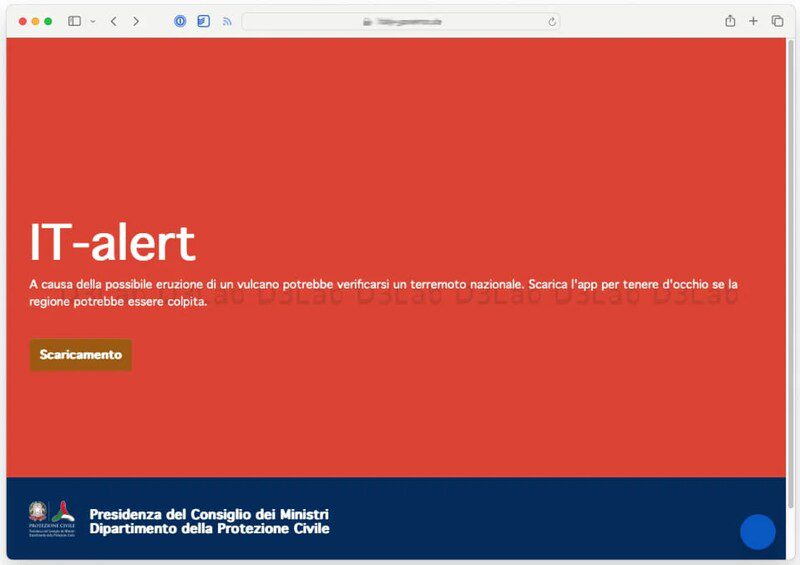
Now, here’s where iOS’ security comes in handy. The button on the page will redirect iOS users to the real IT-alert site.
However, if Android users were to click on the download button, they’d directly receive ‘IT-Alert.apk,’ which installs the SpyNote malware on the device.
This grants the attackers all sorts of dangerous and invasive actions on the compromised device. They achieve that through the app as it asks for permission to work in the background.

Aside from acting as spyware, SpyNote can do a lot more. It can also steal user credentials when the user opens any app that requires them.
This includes social media applications, cryptocurrency wallets, as well as any banking software. Other capabilities include keylogging, taking screenshots, recording calls, and tracking GPS location.
Italian Android Users Beware – They’re Targetting You
The SpyNote malware saw the light back in 2022 when threat actors started selling it through Telegram. Now, it seems that it’s being put to use through various methods.
If you receive such notifications or emails, make sure to visit the real site manually. Never download a link from an untrusted source – You never know who’s behind it.





