macOS at Risk – Cryptomining Malware Spreading Among Peers
macOS devices are widely known to be very secure as Apple implements all the necessary precautions to protect its users. However, most individuals look to bypass these restrictions, leading to some severe consequences. That’s exactly the case now, as trojanized versions of legitimate applications have been seen in the wild lately.

Limiting what its customers get to download elevates their security. But when the users keep tampering with that, malware is bound to take root. We’re referring to getting apps through torrenting platforms such as uTorrent.
The XMRig coin miner is being executed through Final Cut Pro, a video editing software from Apple through torrenting websites. What’s going on, and what’s at risk? Here’s what we know.
macOS Security – Safe Until Tampered With
Limiting what the users get to download on macOS devices has kept the devices’ “secure” reputation intact for quite some time now.
Apple doesn’t allow its customers to get their applications from untrusted websites or sources. They can only do so via the official App Store.
However, lately, these restrictions have been fading as time goes by. Users can even get “Torrenting” clients on their macOS, regardless of the consequences.
Torrent files, the BitTorrent technology, and the torrent software for Mac are completely safe and legal. Unfortunately, the problem lies in the files the users download.
Not only do a lot of them violate copyright laws, but they might also host malware. This is where cybercriminals step in.
In a campaign that has been going on since 2019, threat actors were spreading trojanized versions of legitimate applications to inject cryptocurrency mining malware on macOS systems.
According to Jamf Threat Labs, the crypto miner is XMRig, and it takes root within the Final Cut Pro video-editing app, which contains an unauthorized modification.
“This malware makes use of the Invisible Internet Project (i2p) […] to download malicious components and send mined currency to the attacker’s wallet.”
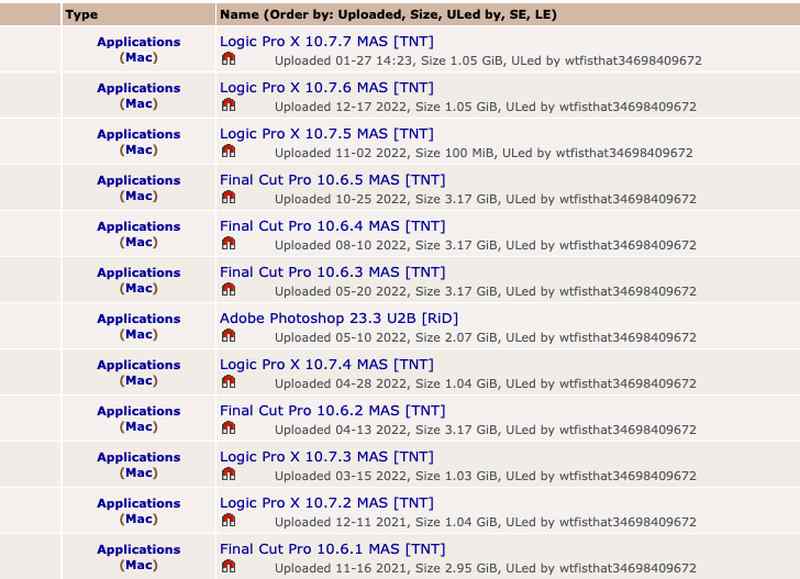
It all started in 2019 when the cryptojacking apps were traced back to the Pirate Bay. You can find the list of applications in the following image:
In the years following the initial release, researchers witnessed a huge evolution in the campaign’s sophistication and stealth.
One of these elevated evasion techniques would be creating a shell script that can monitor the victims’ running processes.
This can be easily disabled through the Activity Monitor as the user can terminate the mining processes on the spot. That, of course, if and only if he/she discovers the miner’s presence.
macOS at Risk – Torrenting Goes Malicious
The malware’s ability to lurk within your system makes it very dangerous. Not just because it can siphon cryptocurrency but also because you cannot detect it without manually checking.
Unfortunately, most users out there like to experiment with cracked software, which is exactly how this malware got distributed.
Stick to the legit stuff, guys; it’s safer for you and every peer who might fall into the same torrenting swarm. Also, use a VPN when you download your torrent files.





